Find the Best Cosmetic Hospitals — Choose with Confidence
Discover top cosmetic hospitals in one place and take the next step toward the look you’ve been dreaming of.
“Your confidence is your power — invest in yourself, and let your best self shine.”
Compare • Shortlist • Decide smarter — works great on mobile too.
Introduction
Software Composition Analysis (SCA) tools are designed to identify, track, and manage open-source components used within applications. These tools scan codebases to detect third-party libraries, dependencies, and packages, helping organizations uncover vulnerabilities, licensing risks, and outdated components. Since modern applications rely heavily on open-source software, SCA tools have become essential for maintaining security, compliance, and transparency.
In today’s development landscape, where supply chain risks and dependency vulnerabilities are increasing, SCA tools play a critical role in DevSecOps strategies. They provide continuous monitoring, automated alerts, and policy enforcement to ensure that applications remain secure throughout their lifecycle.
Common use cases include:
- Identifying vulnerable open-source dependencies
- Managing software licenses and compliance
- Monitoring dependency updates and risks
- Generating Software Bill of Materials (SBOM)
- Integrating security checks into CI/CD pipelines
What buyers should evaluate:
- Depth of dependency scanning
- Vulnerability database accuracy
- License compliance capabilities
- Integration with CI/CD pipelines
- SBOM generation support
- Automation and alerting features
- Ease of integration with development workflows
- Reporting and analytics capabilities
- Scalability for large projects
Best for: Security teams, developers, DevOps engineers, compliance teams, and enterprises managing complex software supply chains.
Not ideal for: Small projects with minimal external dependencies or teams that do not require strict compliance and governance.
Key Trends in Software Composition Analysis (SCA) Tools
- Increasing focus on software supply chain security
- Automated SBOM generation becoming standard
- Integration with DevSecOps pipelines
- AI-assisted vulnerability prioritization
- Real-time monitoring of dependencies
- Improved license compliance tracking
- Expansion into container and infrastructure scanning
- Enhanced reporting and risk analytics
- Growing importance of policy enforcement
How We Selected These Tools (Methodology)
- Evaluated industry adoption and credibility
- Assessed dependency scanning capabilities
- Reviewed vulnerability detection accuracy
- Considered license compliance features
- Analyzed integration with DevOps tools
- Checked scalability for enterprise use
- Included both open-source and commercial tools
- Focused on developer usability and automation
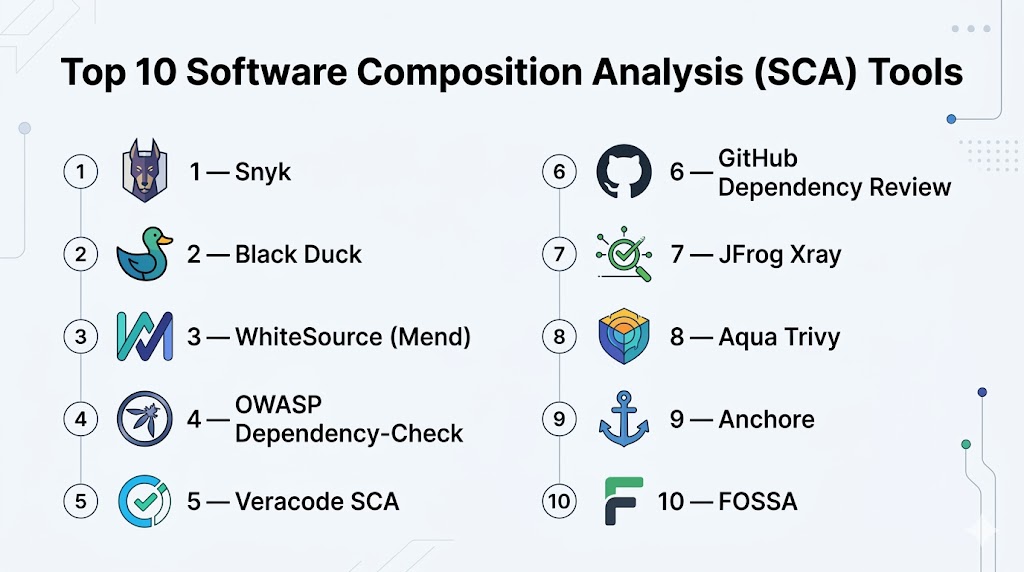
Top 10 Software Composition Analysis (SCA) Tools Tools
#1 — Snyk
Short description: A developer-first security platform that focuses on identifying vulnerabilities in open-source dependencies and fixing them quickly.
Key Features
- Dependency vulnerability scanning
- Automated fix suggestions
- License compliance checks
- Integration with CI/CD
- Container scanning
- Continuous monitoring
- Developer-friendly interface
Pros
- Easy to use
- Strong developer focus
Cons
- Premium features can be costly
- Requires integration setup
Platforms / Deployment
Cloud
Security & Compliance
SSO, RBAC
Integrations & Ecosystem
- Git platforms
- CI/CD pipelines
- Dev tools
Support & Community
Strong documentation and active community.
#2 — Black Duck
Short description: Enterprise-grade SCA tool focused on security and compliance for large organizations.
Key Features
- Open-source risk management
- License compliance
- Vulnerability detection
- SBOM generation
- Policy enforcement
- Reporting tools
- Continuous monitoring
Pros
- Strong compliance features
- Enterprise-ready
Cons
- Expensive
- Complex implementation
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- DevOps tools
- CI/CD pipelines
Support & Community
Enterprise-level support.
#3 — WhiteSource (Mend)
Short description: A security platform that helps manage open-source risks and compliance.
Key Features
- Vulnerability scanning
- License compliance
- Automated remediation
- Policy enforcement
- CI/CD integration
- Dependency tracking
Pros
- Strong automation
- Easy integration
Cons
- Paid plans required for advanced features
- Interface complexity
Platforms / Deployment
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- Dev tools
- Repositories
Support & Community
Professional support available.
#4 — OWASP Dependency-Check
Short description: Open-source SCA tool for identifying vulnerabilities in project dependencies.
Key Features
- Dependency scanning
- Vulnerability detection
- Open-source
- CI/CD integration
- Reporting
- Multi-language support
Pros
- Free
- Easy to integrate
Cons
- Limited enterprise features
- Requires manual tuning
Platforms / Deployment
Windows / macOS / Linux
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- Build tools
- CI/CD
Support & Community
Strong open-source community.
#5 — Veracode SCA
Short description: Cloud-based SCA tool focused on security and compliance.
Key Features
- Vulnerability detection
- License risk management
- Policy enforcement
- CI/CD integration
- Reporting dashboards
Pros
- Strong security focus
- Cloud-native
Cons
- Costly
- Limited customization
Platforms / Deployment
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- DevOps tools
- Security workflows
Support & Community
Enterprise support available.
#6 — GitHub Dependency Review
Short description: Built-in dependency analysis tool within GitHub repositories.
Key Features
- Dependency scanning
- Vulnerability alerts
- Pull request integration
- Dependency insights
- Security alerts
Pros
- Easy to use
- Integrated into workflow
Cons
- Limited outside GitHub
- Basic features
Platforms / Deployment
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- GitHub ecosystem
- CI/CD
Support & Community
Large user base.
#7 — JFrog Xray
Short description: Security tool focused on scanning dependencies and artifacts.
Key Features
- Dependency scanning
- Artifact analysis
- Policy enforcement
- CI/CD integration
- Vulnerability detection
Pros
- Strong artifact scanning
- Enterprise-ready
Cons
- Complex setup
- Paid solution
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- DevOps tools
- Artifact repositories
Support & Community
Professional support.
#8 — Aqua Trivy
Short description: Lightweight open-source tool for vulnerability scanning in containers and dependencies.
Key Features
- Dependency scanning
- Container scanning
- Fast performance
- Open-source
- CI/CD integration
Pros
- Lightweight
- Easy to use
Cons
- Limited enterprise features
- Basic reporting
Platforms / Deployment
Windows / macOS / Linux
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- DevOps tools
- Container environments
Support & Community
Active community.
#9 — Anchore
Short description: SCA tool focused on container and software supply chain security.
Key Features
- Container scanning
- Policy enforcement
- Vulnerability detection
- SBOM support
- CI/CD integration
Pros
- Strong container support
- Open-source option
Cons
- Setup complexity
- Learning curve
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- Container tools
- DevOps pipelines
Support & Community
Growing support.
#10 — FOSSA
Short description: SCA platform focused on open-source compliance and security.
Key Features
- License compliance
- Vulnerability detection
- Policy management
- Reporting tools
- CI/CD integration
Pros
- Strong compliance features
- Easy integration
Cons
- Paid tool
- Limited customization
Platforms / Deployment
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- Dev tools
- CI/CD
Support & Community
Professional support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Snyk | Developers | Cloud | Cloud | Fix suggestions | N/A |
| Black Duck | Enterprise | Cross-platform | Hybrid | Compliance focus | N/A |
| Mend | Automation | Cloud | Cloud | Remediation | N/A |
| OWASP Dependency-Check | Open-source | Cross-platform | Local | Free scanning | N/A |
| Veracode | Security | Cloud | Cloud | Policy enforcement | N/A |
| GitHub Dependency Review | GitHub users | Web | Cloud | Built-in scanning | N/A |
| JFrog Xray | Artifacts | Cross-platform | Hybrid | Artifact analysis | N/A |
| Trivy | Containers | Cross-platform | Local | Lightweight | N/A |
| Anchore | Containers | Cross-platform | Hybrid | SBOM support | N/A |
| FOSSA | Compliance | Cloud | Cloud | License tracking | N/A |
Evaluation & Scoring of Software Composition Analysis (SCA) Tools
| Tool Name | Core | Ease | Integrations | Security | Performance | Support | Value | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Snyk | 9 | 9 | 10 | 9 | 9 | 9 | 8 | 9.1 |
| Black Duck | 10 | 7 | 9 | 10 | 9 | 9 | 7 | 9.0 |
| Mend | 9 | 8 | 9 | 9 | 8 | 8 | 8 | 8.6 |
| Dependency-Check | 7 | 8 | 7 | 7 | 8 | 7 | 10 | 7.9 |
| Veracode | 9 | 8 | 8 | 10 | 8 | 9 | 7 | 8.7 |
| GitHub | 7 | 9 | 8 | 8 | 8 | 9 | 9 | 8.2 |
| Xray | 9 | 7 | 9 | 9 | 8 | 8 | 7 | 8.4 |
| Trivy | 8 | 9 | 8 | 8 | 9 | 8 | 10 | 8.7 |
| Anchore | 8 | 7 | 8 | 9 | 8 | 7 | 8 | 8.0 |
| FOSSA | 8 | 8 | 8 | 9 | 8 | 8 | 7 | 8.2 |
How to interpret scores:
These scores represent a comparative evaluation across features, usability, and ecosystem support. Higher scores indicate well-rounded tools, while lower scores may still suit niche use cases. Always select based on your specific needs rather than rankings alone.
Which Software Composition Analysis (SCA) Tools Tool Is Right for You?
Solo / Freelancer
- Best: Trivy, Dependency-Check
SMB
- Best: Snyk, Mend
Mid-Market
- Best: Snyk, JFrog Xray
Enterprise
- Best: Black Duck, Veracode
Budget vs Premium
- Budget: Trivy, Dependency-Check
- Premium: Black Duck, Veracode
Feature Depth vs Ease of Use
- Easy: Snyk
- Advanced: Black Duck
Integrations & Scalability
- Choose tools with strong CI/CD support
Security & Compliance Needs
- Enterprises should prioritize compliance-focused tools
Frequently Asked Questions (FAQs)
What are SCA tools?
They analyze open-source dependencies for vulnerabilities and risks.
Why are they important?
They help secure the software supply chain.
Are they free?
Some are open-source, others are paid.
Do they detect vulnerabilities?
Yes, that is their main function.
Can they integrate with CI/CD?
Yes, most tools support integration.
Do they support compliance?
Many tools include license compliance features.
Are they accurate?
Accuracy depends on the tool and configuration.
Can small teams use them?
Yes, many tools are suitable for small teams.
Do they replace security testing?
No, they complement other security tools.
Which tool is best?
It depends on your needs.
Conclusion
Software Composition Analysis tools are critical for managing open-source risks and ensuring software security. They help organizations identify vulnerabilities, enforce compliance, and maintain visibility into dependencies across applications. As software supply chains become more complex, these tools play an increasingly important role in development workflows. While some tools focus on lightweight scanning, others provide enterprise-grade security and governance features. The best choice depends on your team size, compliance requirements, and development environment. Instead of relying on popularity alone, evaluate how well a tool integrates into your workflow and supports your security goals. Start by testing a few tools and select the one that offers the best balance of usability, performance, and protection.