Find the Best Cosmetic Hospitals — Choose with Confidence
Discover top cosmetic hospitals in one place and take the next step toward the look you’ve been dreaming of.
“Your confidence is your power — invest in yourself, and let your best self shine.”
Compare • Shortlist • Decide smarter — works great on mobile too.
Introduction
Cloud Security Posture Management (CSPM) is a category of security tools designed to identify misconfigurations and compliance risks in the cloud. As organizations migrate from on-premises data centers to environments like AWS, Azure, and Google Cloud, the complexity of managing permissions and settings grows exponentially. CSPM tools act as a continuous monitor, scanning your cloud infrastructure to ensure that every bucket, virtual machine, and network gateway is configured according to industry best practices and security standards.
The importance of CSPM cannot be overstated in the modern era of digital transformation. The vast majority of cloud-based data breaches are not caused by sophisticated hacking but by simple human error—such as leaving a storage bucket public or misconfiguring a firewall rule. CSPM provides the visibility needed to catch these errors before they can be exploited. It moves security from a manual, periodic check to an automated, constant state of vigilance.
Real-world use cases:
- Misconfiguration Detection: Finding unencrypted databases or open ports that expose internal data to the public internet.
- Compliance Auditing: Automatically checking cloud environments against frameworks like SOC 2, HIPAA, or PCI DSS.
- Inventory Management: Maintaining a real-time list of every asset across multiple cloud accounts and regions.
- Incident Response: Alerting security teams the moment a change occurs that lowers the security posture.
- IAM Risk Assessment: Identifying “over-privileged” users who have more access than they need for their job.
Evaluation criteria for buyers:
- Multi-Cloud Support: The ability to manage AWS, Azure, and GCP through a single pane of glass.
- Ease of Deployment: Whether the tool requires agents to be installed on every machine or uses API-based scanning.
- Remediation Guidance: Does the tool just find problems, or does it explain exactly how to fix them (or fix them automatically)?
- Compliance Frameworks: The number of pre-built regulatory templates available for automated auditing.
- Integration Capabilities: How well it connects with Slack, Jira, and CI/CD pipelines.
- Real-Time Monitoring: The speed at which a new misconfiguration is detected and reported.
- Infrastructure as Code (IaC) Scanning: The ability to find errors in templates before they are even deployed to the cloud.
- Contextual Awareness: Does the tool understand the relationship between assets to prioritize high-risk vulnerabilities?
- Reporting and Dashboards: The clarity of executive-level summaries versus deep-dive technical logs.
- Total Cost of Ownership: The balance of the subscription fee against the reduction in manual security labor.
Mandatory Paragraph
- Best for: Enterprises with complex multi-cloud environments, financial institutions with strict compliance needs, and fast-growing SaaS companies looking to automate infrastructure security.
- Not ideal for: Small businesses with a single, simple cloud account or teams that do not have the capacity to act on the security alerts generated by the system.
Key Trends in Cloud Security Posture Management
- Shift-Left Integration: Modern CSPM tools are moving earlier in the development lifecycle, scanning Infrastructure as Code (IaC) files to stop misconfigurations before they reach production.
- Agentless Scanning: There is a massive trend toward “agentless” technology that uses cloud APIs and disk snapshots to scan for risks without requiring software installation on every server.
- CNAPP Convergence: CSPM is increasingly being merged into broader Cloud-Native Application Protection Platforms (CNAPP) that include container and workload security.
- Automated Remediation: Tools are evolving from “alert-only” systems to platforms that can automatically fix high-risk errors, such as closing an open port or rotating an exposed key.
- Graph-Based Analysis: Using graph databases to visualize the complex relationships between assets, helping security teams understand “attack paths” that lead to sensitive data.
- Identity-Centric Security: A growing focus on Cloud Infrastructure Entitlement Management (CIEM) within the CSPM toolset to find and reduce excessive permissions.
- AI-Driven Prioritization: Leveraging machine learning to filter out “alert fatigue” by highlighting the 1% of risks that actually pose a critical threat.
- Data Security Posture Management (DSPM): Expanding CSPM logic specifically to data assets to ensure sensitive customer information is always encrypted and protected.
How We Selected These Tools (Methodology)
To select the top 10 CSPM tools, we conducted an analysis focused on practical utility and market performance. Our methodology prioritized the following logic:
- Feature Maturity: We looked for tools that have moved beyond basic scanning to offer deep contextual analysis and automated fixes.
- Platform Coverage: We prioritized solutions that offer native, high-quality support across all major public cloud providers.
- Market Adoption: We evaluated tools based on their reputation within the cybersecurity community and their usage by global companies.
- Technical Innovation: We favored platforms that have pioneered modern techniques like agentless scanning and graph-based risk visualization.
- Customer Feedback: We analyzed the reliability of the tools in real-world scenarios, focusing on the accuracy of alerts and ease of management.
- Security Posture Signals: We assessed the vendor’s own commitment to security and their frequency of feature updates.
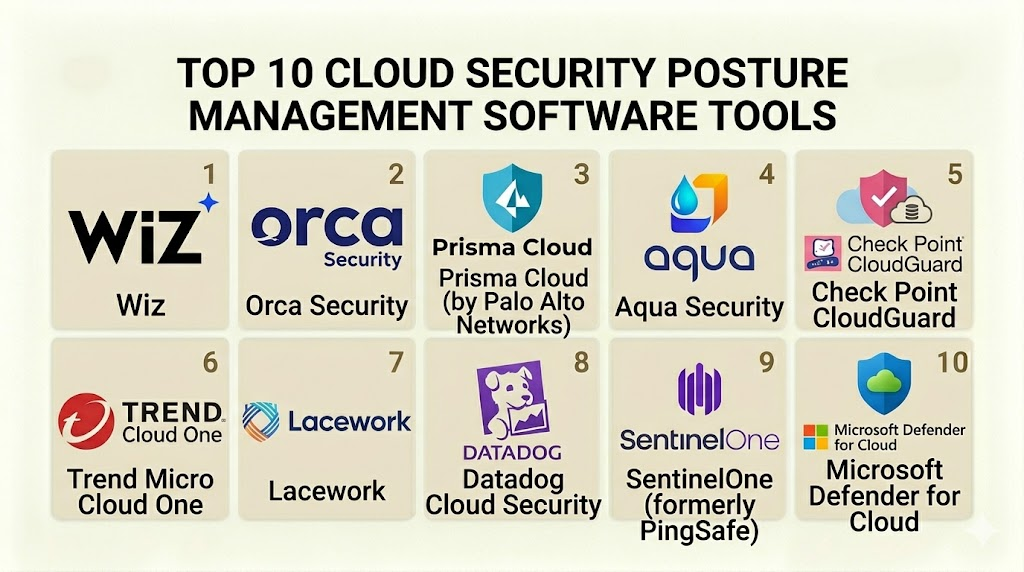
Top 10 Cloud Security Posture Management Software Tools
#1 — Wiz
Short description: Wiz is widely considered a pioneer in agentless cloud security. It provides a complete view of cloud risks by connecting to your environment via API and scanning every layer without any performance impact.
Key Features
- Wiz Graph: Visualizes the entire cloud environment to show how vulnerabilities, identities, and misconfigurations can be linked together.
- Agentless Scanning: Uses cloud-native snapshots to scan disks for vulnerabilities and secrets without installing software.
- IaC Scanning: Scans Terraform, CloudFormation, and other templates to find errors during the coding phase.
- Inventory & Visibility: Provides a real-time, searchable inventory of every single cloud asset across all accounts.
- Compliance Center: Offers pre-built dashboards for dozens of regulatory frameworks like SOC 2 and GDPR.
- Security Graph Heatmap: Prioritizes issues by showing which risks are “exposed” to the public internet.
Pros
- Incredibly fast time-to-value; you can see your entire security posture in minutes.
- Contextual analysis significantly reduces alert fatigue by focusing on reachable threats.
Cons
- The premium features come with a high price point that may be out of reach for small startups.
- Heavy focus on cloud-native might make it less ideal for legacy hybrid-cloud setups.
Platforms / Deployment
- AWS / Azure / Google Cloud / OCI / Alibaba Cloud
- SaaS
Security & Compliance
- SSO, MFA, RBAC, and granular API permissions.
- SOC 2 Type II, ISO 27001, FedRAMP (in process).
Integrations & Ecosystem
Wiz integrates with the entire modern developer stack to ensure security is part of the workflow.
- Slack and Microsoft Teams for alerting.
- Jira and ServiceNow for ticket management.
- GitHub, GitLab, and Bitbucket for IaC scanning.
- Splunk and Datadog for log analysis.
Support & Community
Wiz offers a highly rated customer success program and extensive documentation. Their technical support is known for being responsive and deeply technical.
#2 — Orca Security
Short description: Orca Security is known for its “SideScanning” technology, which allows it to see deep inside cloud workloads without agents, providing a comprehensive view of the entire cloud estate.
Key Features
- SideScanning Technology: Reads cloud block storage out-of-band to detect vulnerabilities, malware, and misconfigurations.
- Risk Prioritization: Uses a unified data model to score risks based on the sensitivity of the data and the exposure of the asset.
- Data Security Posture: Specifically identifies where sensitive data like PII or credit card numbers are stored and if they are at risk.
- API Security: Automatically discovers and monitors API endpoints to find vulnerabilities or exposed keys.
- Shift-Left Security: Integrates with CI/CD pipelines to scan container images and IaC templates.
- Compliance Management: Provides continuous monitoring for over 40 different compliance standards.
Pros
- Complete 100% visibility of all workloads without the “blind spots” often found with agent-based tools.
- Very low operational overhead since there are no agents to deploy or update.
Cons
- Can generate a high volume of data that requires a dedicated team to manage and filter.
- Remediation is largely focused on guidance rather than fully automated “one-click” fixes.
Platforms / Deployment
- AWS / Azure / Google Cloud
- SaaS
Security & Compliance
- MFA, SSO, and encrypted data handling.
- SOC 2, ISO 27001, HIPAA compliance reporting.
Integrations & Ecosystem
Orca is designed to be the central security hub for cloud-native teams.
- PagerDuty and Opsgenie.
- Jenkins and CircleCI.
- Azure DevOps.
- Tenable and Qualys for vulnerability data.
Support & Community
Orca provides excellent technical documentation and a “Cloud Security Podcast” that keeps the community informed on the latest threats.
#3 — Prisma Cloud (by Palo Alto Networks)
Short description: Prisma Cloud is one of the most comprehensive Cloud-Native Application Protection Platforms (CNAPP) on the market, combining CSPM with workload and network security.
Key Features
- Full-Stack Visibility: Covers everything from the underlying cloud infrastructure to the running application code.
- Policy Library: Includes thousands of pre-configured policies based on industry standards and Palo Alto’s research.
- Automated Remediation: Can be configured to automatically fix common misconfigurations, such as closing insecure ports.
- Identity and Entitlement Management: Finds users with excessive permissions and suggests “least-privilege” policies.
- Network Visualization: Shows live traffic flows to identify unauthorized communication between services.
- Bridgecrew Integration: Offers world-class IaC scanning to secure infrastructure before it is deployed.
Pros
- Ideal for large enterprises that need a single tool for CSPM, CWPP, and network security.
- Deep integration with Palo Alto’s broader security ecosystem.
Cons
- The platform is massive and can be complex to learn for smaller teams.
- Requires a more significant configuration effort compared to simpler agentless tools.
Platforms / Deployment
- AWS / Azure / GCP / OCI / Alibaba / Private Cloud
- SaaS / Hybrid
Security & Compliance
- Enterprise-grade RBAC, SSO, and SAML.
- Extensive list of global compliance certifications.
Integrations & Ecosystem
Broadest integration list in the category due to its enterprise focus.
- Terraform and Ansible.
- All major CI/CD platforms.
- ServiceNow and Splunk.
- AWS Security Hub.
Support & Community
Benefit from Palo Alto’s global support network, including 24/7 technical assistance and an extensive partner network.
#4 — Aqua Security
Short description: Aqua Security focuses heavily on the entire lifecycle of cloud-native applications, with strong CSPM capabilities that specialize in container and Kubernetes security.
Key Features
- Unified Security: Manages security for VMs, containers, and serverless functions from one place.
- Kubernetes Assurance: Provides deep scanning of K8s clusters to find misconfigured roles or insecure defaults.
- Digital Signatures: Ensures that only authorized code and images are allowed to run in your cloud environment.
- Compliance Templates: Offers specialized reporting for the CIS Benchmark and other container-specific standards.
- Risk Explorer: A visual tool that maps out the relationships between cloud resources to find potential attack paths.
- Malware Detection: Scans cloud storage and running workloads for signs of malicious software.
Pros
- Arguably the best choice for organizations that are “container-first” or use Kubernetes heavily.
- Strong focus on the developer experience with native CI/CD plugins.
Cons
- The CSPM features are strong, but the tool is most effective when used for its workload protection features too.
- Setup for non-containerized environments is less intuitive.
Platforms / Deployment
- AWS / Azure / GCP / OCI / OpenShift
- SaaS / Self-hosted
Security & Compliance
- Role-based access and secure secret management.
- SOC 2, ISO 27001.
Integrations & Ecosystem
Aqua is built for the DevOps world.
- Docker and Kubernetes.
- Prometheus for monitoring.
- Jira and Slack.
- GitHub Actions.
Support & Community
Aqua has a very active community and provides a wealth of educational content on cloud-native security best practices.
#5 — Check Point CloudGuard
Short description: CloudGuard provides automated security posture management and multi-cloud compliance, leveraging Check Point’s decades of network security expertise.
Key Features
- High-Fidelity Posture Management: Uses the “GSL” (Governance Specification Language) to create custom security rules easily.
- Intelligence and Threat Hunting: Analyzes cloud logs to find behavioral anomalies that suggest a breach.
- IAM Safety: Provides an additional layer of protection for high-risk IAM actions by requiring “just-in-time” approval.
- Compliance Engine: Offers over 300 built-in cloud security best practice checks.
- Cloud Inventory: Automatically discovers new assets as they are created across different cloud regions.
- Serverless Security: Specialized protection for AWS Lambda and Azure Functions.
Pros
- Excellent for organizations that already use Check Point for their network firewalls.
- Highly customizable rule engine allows for very specific security requirements.
Cons
- The user interface can feel more like a legacy security tool compared to modern SaaS platforms.
- Higher learning curve to master the custom GSL language.
Platforms / Deployment
- AWS / Azure / GCP / OCI / Alibaba
- SaaS
Security & Compliance
- Standard enterprise security controls including MFA and SSO.
- SOC 2, ISO 27001.
Integrations & Ecosystem
Integrates well with enterprise IT and security operations.
- Azure Sentinel.
- AWS Security Hub.
- Splunk and Sumo Logic.
- Tufin for security policy management.
Support & Community
Access to Check Point’s global support centers and a large community of certified security professionals.
#6 — Trend Micro Cloud One
Short description: Cloud One is a multi-service platform designed to provide a broad range of security for cloud builders, with CSPM as a core component.
Key Features
- Conformity Service: The specific part of Cloud One that handles CSPM and compliance.
- Real-time Visibility: Provides a constant feed of security checks across all cloud accounts.
- Remediation Guides: Includes step-by-step instructions (and scripts) for fixing every identified risk.
- Template Scanning: Scans CloudFormation and Terraform templates for errors before deployment.
- Custom Profiles: Allows teams to set specific security baselines for different projects or departments.
- Workload Protection: Seamlessly integrates with Trend Micro’s industry-leading server security.
Pros
- Very easy to get started with a high number of out-of-the-box checks.
- The remediation guides are among the best in the industry for educating junior staff.
Cons
- The platform can feel fragmented because it is made up of several different services.
- Doesn’t offer the same “graph-based” context as some of the newer competitors.
Platforms / Deployment
- AWS / Azure / Google Cloud
- SaaS
Security & Compliance
- Multi-factor authentication and secure identity management.
- SOC 2, ISO 27001, PCI DSS.
Integrations & Ecosystem
Trend Micro has a long history of enterprise integrations.
- ServiceNow and Jira.
- Slack and Microsoft Teams.
- Amazon GuardDuty.
- CI/CD pipeline tools.
Support & Community
Trend Micro provides robust enterprise support and a large knowledge base of cloud security articles.
#7 — Lacework
Short description: Lacework uses a unique “Polygraph” technology to automatically learn the behavior of your cloud environment, identifying risks and anomalies without manual rule-writing.
Key Features
- Polygraph Technology: Maps every entity and communication in your cloud to find behavioral changes.
- Automated Risk Prioritization: Focuses on the most critical threats by understanding the context of an alert.
- Compliance Monitoring: Provides continuous auditing against CIS, PCI, and SOC 2.
- Host and Container Security: Combines posture management with deep workload visibility.
- Cloud Trail Analysis: Monitors cloud provider logs for unauthorized account activity.
- IaC Integration: Finds security issues in the infrastructure code used to build the cloud.
Pros
- Extremely low manual effort because the system “learns” what is normal for your cloud.
- Excellent for finding “unknown” threats that don’t match a specific signature or rule.
Cons
- The “black box” nature of the behavioral learning can make it harder for some teams to understand why an alert was triggered.
- Pricing is often based on the volume of data processed, which can be difficult to predict.
Platforms / Deployment
- AWS / Azure / Google Cloud
- SaaS
Security & Compliance
- Secure SSO and MFA.
- SOC 2 Type II, ISO 27001.
Integrations & Ecosystem
Lacework is built for modern, high-velocity cloud teams.
- Terraform and Kubernetes.
- Snowflake for data analysis.
- Jira and Slack.
- VictorOps and PagerDuty.
Support & Community
Lacework offers strong technical support and a growing community of “Laceworkers” who share best practices.
#8 — Datadog Cloud Security
Short description: Datadog leverages its massive popularity in observability to provide a security tool that integrates posture management directly into the developer’s monitoring dashboard.
Key Features
- Unified Monitoring: See security alerts alongside performance metrics and application logs.
- Cloud Security Management: Scans cloud resources for misconfigurations based on 400+ out-of-the-box rules.
- Workload Security: Monitors file integrity and process execution on servers and containers.
- Postgres and Database Monitoring: Deep visibility into the security settings of managed databases.
- Compliance Tracking: Continuous monitoring of progress against major regulatory frameworks.
- Custom Detection Rules: An easy-to-use editor for creating security rules specific to your business logic.
Pros
- If you already use Datadog for monitoring, adding CSPM is a simple “one-click” experience.
- Provides incredible context by showing how a security risk might be impacting application performance.
Cons
- The CSPM features are newer and less mature than those of specialist vendors like Wiz or Orca.
- Costs can escalate quickly if you have a massive amount of logs and metrics.
Platforms / Deployment
- AWS / Azure / GCP / Alibaba / OCI
- SaaS
Security & Compliance
- Robust SSO, MFA, and data encryption.
- SOC 2, ISO 27001, FedRAMP.
Integrations & Ecosystem
Datadog has one of the largest integration libraries in the world.
- Over 500+ built-in integrations for nearly every cloud service.
- Slack, PagerDuty, and Jira.
- Terraform and Ansible.
Support & Community
Huge community of developers and engineers. Datadog provides extensive training through “Datadog Learning Center.”
#9 — SentinelOne (formerly PingSafe)
Short description: Following its acquisition of PingSafe, SentinelOne provides an advanced CSPM solution that focuses on offensive security context and vulnerability research.
Key Features
- Offensive Security Engine: Simulates how an attacker would view your cloud to find the most dangerous paths.
- Secrets Scanning: Scans for exposed passwords, API keys, and certificates in cloud storage.
- Vulnerability Management: Identifies unpatched software across all cloud virtual machines.
- Real-time Compliance: Provides a live score for your cloud’s compliance with global standards.
- Graph-based Risk Map: Visualizes the “blast radius” of a potential security incident.
- Unified Endpoint and Cloud: Part of the broader SentinelOne Singularity platform.
Pros
- Provides a “hacker’s eye view” of the cloud, which helps in prioritizing what to fix first.
- Excellent for organizations that want to consolidate endpoint and cloud security under one vendor.
Cons
- As a newly integrated product, the user experience is still evolving.
- Focused primarily on large enterprises with existing SentinelOne deployments.
Platforms / Deployment
- AWS / Azure / Google Cloud
- SaaS
Security & Compliance
- Military-grade security controls.
- SOC 2, ISO 27001.
Integrations & Ecosystem
Part of the Singularity marketplace.
- Splunk and IBM QRadar.
- Slack and Microsoft Teams.
- CI/CD pipeline integrations.
Support & Community
Supported by SentinelOne’s global incident response and technical support teams.
#10 — Microsoft Defender for Cloud
Short description: Microsoft’s native security posture management tool for Azure, which has expanded to provide first-class support for AWS and Google Cloud as well.
Key Features
- Secure Score: A simple, gamified metric that helps teams track their security progress over time.
- Multi-Cloud CSPM: Full visibility into AWS and GCP security settings from the Azure portal.
- Native Remediation: Offers “Fix” buttons that automatically resolve security issues in Azure.
- Regulatory Compliance Dashboard: Tracks compliance with ISO, SOC, and various government standards.
- Just-In-Time (JIT) VM Access: Reduces the attack surface by opening management ports only when needed.
- Cloud Security Explorer: A graph-based tool for hunting risks across multi-cloud environments.
Pros
- The absolute best choice for Azure-heavy environments.
- “Free” tier provides basic posture management, with the paid “Defender” tier adding advanced features.
Cons
- While it supports multi-cloud, the experience for AWS and GCP is not as deep as the native Azure experience.
- The interface can be overwhelming as it is part of the massive Azure portal.
Platforms / Deployment
- Azure / AWS / GCP / On-premises
- SaaS
Security & Compliance
- Integrated with Microsoft Entra ID (formerly Azure AD).
- Highest level of global compliance certifications.
Integrations & Ecosystem
Native integration with the entire Microsoft ecosystem.
- Microsoft Sentinel (SIEM).
- Azure DevOps.
- Microsoft Teams.
- Log Analytics workspaces.
Support & Community
World-class support from Microsoft and a vast global network of Azure security partners.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. Wiz | Multi-Cloud Context | AWS, Azure, GCP, OCI | SaaS | Wiz Security Graph | 4.9/5 |
| 2. Orca Security | Workload Visibility | AWS, Azure, GCP | SaaS | SideScanning Technology | 4.8/5 |
| 3. Prisma Cloud | Global Enterprise | Multi-Cloud + Private | Hybrid | Full-Stack CNAPP | 4.7/5 |
| 4. Aqua Security | Kubernetes/Containers | Multi-Cloud + K8s | Hybrid | K8s Assurance | 4.6/5 |
| 5. Check Point | Network-heavy Cloud | Multi-Cloud + Alibaba | SaaS | GSL Custom Rules | 4.4/5 |
| 6. Trend Micro | DevOps Education | AWS, Azure, GCP | SaaS | Remediation Guides | 4.5/5 |
| 7. Lacework | Behavioral Anomaly | AWS, Azure, GCP | SaaS | Polygraph Learning | 4.6/5 |
| 8. Datadog | Monitoring + Security | Multi-Cloud | SaaS | Observability Context | 4.5/5 |
| 9. SentinelOne | Offensive Context | AWS, Azure, GCP | SaaS | Offensive Engine | 4.4/5 |
| 10. Microsoft Defender | Azure-centric Multi-Cloud | Azure, AWS, GCP | SaaS | Secure Score | 4.6/5 |
Evaluation & Scoring of CSPM Tools
The following table provides a weighted scoring of each tool based on the criteria that matter most to modern security leaders.
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| Wiz | 10 | 10 | 9 | 9 | 10 | 9 | 7 | 9.15 |
| Orca Security | 10 | 9 | 8 | 9 | 10 | 9 | 8 | 9.05 |
| Prisma Cloud | 10 | 6 | 10 | 10 | 9 | 9 | 7 | 8.55 |
| Aqua Security | 9 | 7 | 9 | 9 | 9 | 8 | 8 | 8.40 |
| Check Point | 8 | 6 | 8 | 10 | 8 | 9 | 8 | 7.95 |
| Trend Micro | 8 | 8 | 8 | 9 | 8 | 9 | 8 | 8.15 |
| Lacework | 9 | 7 | 8 | 9 | 9 | 8 | 8 | 8.25 |
| Datadog | 7 | 10 | 10 | 9 | 8 | 9 | 8 | 8.35 |
| SentinelOne | 8 | 7 | 8 | 9 | 9 | 8 | 8 | 8.05 |
| Microsoft Defender | 8 | 9 | 10 | 10 | 8 | 9 | 9 | 8.85 |
Scoring Logic:
- Core (25%): Depth of scanning, context, and remediation.
- Ease (15%): How fast the tool can be deployed and used by a non-expert.
- Integrations (15%): The quality of the API and connection to other tools.
- Total Score: Calculated as $(Core \times 0.25) + (Ease \times 0.15) + …$
Which CSPM Tool Is Right for You?
Solo / Freelancer
If you are an individual consultant or a small developer, Microsoft Defender for Cloud (Free Tier) or the free version of Wiz (if available) is the best starting point. These provide high-level visibility without a massive financial commitment.
SMB
Small and medium-sized businesses should prioritize Datadog Cloud Security or Trend Micro Cloud One. Datadog is excellent if you are already using it for monitoring, while Trend Micro provides the best step-by-step guidance for teams that don’t have a dedicated security expert.
Mid-Market
For companies with a dedicated DevOps team, Orca Security or Lacework provide the most value. These tools offer “agentless” peace of mind and behavioral insights that can help a small team protect a large cloud footprint efficiently.
Enterprise
Large-scale organizations with hundreds of cloud accounts and complex compliance needs should choose between Wiz, Prisma Cloud, or Microsoft Defender for Cloud. Wiz offers the best contextual visibility, Prisma offers the most comprehensive security suite, and Microsoft offers the best value for Azure-heavy environments.
Budget vs Premium
- Budget: Microsoft Defender for Cloud (Free features), Datadog (entry tiers).
- Premium: Wiz, Prisma Cloud, Orca Security.
Feature Depth vs Ease of Use
- High Depth: Prisma Cloud, Check Point CloudGuard.
- High Ease of Use: Wiz, Datadog Cloud Security.
Integrations & Scalability
- Best Integrations: Datadog, Prisma Cloud.
- Best Scalability: Wiz, Microsoft Defender for Cloud.
Security & Compliance Needs
Organizations in banking or healthcare should lean toward Prisma Cloud or Wiz, as they provide the most detailed compliance reports and the deepest level of security auditing for sensitive environments.
Frequently Asked Questions (FAQs)
1. What is the difference between CSPM and a traditional WAF?
A WAF protects against attacks targeting the application code (like SQL injection), while CSPM monitors the security settings of the cloud infrastructure itself (like open ports or unencrypted storage).
2. Can I use a CSPM tool for multi-cloud environments?
Yes, almost all leading CSPM tools like Wiz, Orca, and Prisma Cloud are designed to provide a unified view across AWS, Azure, and Google Cloud simultaneously.
3. Is agentless scanning better than agent-based scanning?
Agentless is generally preferred for CSPM because it provides 100% visibility without needing to install software on every machine, which reduces complexity and performance overhead.
4. How often do CSPM tools scan for misconfigurations?
Most tools offer “near real-time” monitoring by listening to cloud provider configuration logs and performing a full deep scan once or twice a day.
5. Will a CSPM tool automatically fix my security problems?
Many tools offer automated remediation for simple issues (like closing a port), but most teams use the tool for “remediation guidance” to ensure they don’t accidentally break an application.
6. Do CSPM tools help with compliance like SOC 2 or HIPAA?
Yes, this is a core feature. They provide automated audits and dashboards that show exactly which controls you are meeting and where you need to improve to pass an audit.
7. What is “Alert Fatigue” in CSPM?
Alert fatigue happens when a tool generates hundreds of notifications for minor issues, causing security teams to ignore them. Modern tools use “context” to prioritize only the most dangerous alerts.
8. Can CSPM tools see inside my containers or Kubernetes?
Advanced CSPM tools can see the configuration of Kubernetes clusters, and many integrated “CNAPP” platforms can also scan the contents of the containers themselves.
9. Are CSPM tools expensive for small companies?
While premium tools can be costly, many vendors offer tiered pricing based on the number of cloud resources you have, and cloud providers offer native versions at lower costs.
10. Can CSPM detect exposed secrets like API keys?
Yes, top-tier CSPM tools scan storage buckets and machine configurations to find exposed credentials or keys that an attacker could use to escalate their access.
Conclusion
Cloud Security Posture Management is the foundation of a modern cloud security strategy. In an era where a single misclicked setting can lead to a million-dollar breach, the visibility and automation provided by these tools are essential. Whether you choose the agentless simplicity of Wiz, the behavioral intelligence of Lacework, or the enterprise depth of Prisma Cloud, the most important step is to implement a solution that offers continuous, automated oversight.Start by running a free trial or “cloud risk assessment” offered by many of these vendors. This will give you an immediate look at your “Secure Score” and help you prioritize the most critical fixes for your cloud environment.