Find the Best Cosmetic Hospitals — Choose with Confidence
Discover top cosmetic hospitals in one place and take the next step toward the look you’ve been dreaming of.
“Your confidence is your power — invest in yourself, and let your best self shine.”
Compare • Shortlist • Decide smarter — works great on mobile too.
Introduction
Attack Surface Management (ASM) is a continuous security process involving the discovery, analysis, remediation, and monitoring of the cybersecurity vulnerabilities and potential attack vectors that make up an organization’s external-facing digital presence. Unlike traditional vulnerability scanning, which often focuses on known assets within a network, ASM takes an “outside-in” perspective. It mimics the behavior of an attacker to identify every digital asset that is reachable from the internet—including forgotten subdomains, misconfigured cloud buckets, and shadow IT that the security team may not even know exists.
In the modern digital landscape, the perimeter has essentially dissolved. With the explosion of cloud services, remote work, and third-party integrations, an organization’s digital footprint expands daily. ASM provides the visibility required to manage this sprawl, ensuring that every asset is accounted for and secured before a malicious actor can exploit a weakness. It is no longer sufficient to secure only what is on a spreadsheet; security teams must secure what is actually visible to the world.
Real-world use cases:
- Shadow IT Discovery: Finding employee-created cloud instances or staging servers that were never reported to IT.
- Subsidiary Risk Assessment: Identifying security gaps in newly acquired companies or remote branch offices.
- Cloud Leakage Prevention: Detecting publicly accessible storage buckets containing sensitive customer data.
- Digital Supply Chain Monitoring: Assessing the risk introduced by third-party scripts and hosted services.
- Vulnerability Prioritization: Mapping known exploits to high-value, internet-facing assets for immediate patching.
Evaluation criteria for buyers:
- Discovery Accuracy: The ability to find assets accurately without generating excessive false positives.
- Asset Attribution: The capability to prove that a discovered asset actually belongs to the organization.
- Continuous Monitoring: Frequency of scans and real-time alerting on new asset appearances.
- Vulnerability Correlation: Integration of threat intelligence to rank risks by actual exploitability.
- Cloud Native Support: Deep integration with major cloud service providers (AWS, Azure, GCP).
- Ease of Deployment: How quickly the platform can begin discovery without requiring agent installation.
- Shadow IT Identification: Success rate in finding “dark” assets outside of known IP ranges.
- Reporting and Dashboards: Quality of executive and technical views for tracking risk reduction over time.
- Integration Capabilities: Compatibility with existing SIEM, SOAR, and ticketing workflows.
- Global Scanning Coverage: The breadth and geographical distribution of the provider’s scanning infrastructure.
Mandatory Paragraph
- Best for: Enterprise security teams, Chief Information Security Officers (CISOs), and managed service providers (MSPs) responsible for securing vast, fragmented, or rapidly changing digital infrastructures.
- Not ideal for: Small businesses with a single static website and no cloud footprint, or organizations that only require internal network auditing without any internet-facing presence.
Key Trends in Attack Surface Management
- Convergence with Exposure Management: ASM is moving beyond simple discovery to become a core part of Continuous Threat Exposure Management (CTEM) frameworks.
- AI-Powered Attribution: Machine learning is now used to analyze domain registrations, SSL certificates, and hosting patterns to more accurately attribute assets to their parent companies.
- External-to-Internal Mapping: Modern tools are beginning to bridge the gap by showing how an external vulnerability can be used as a pivot point into the internal network.
- API-Centric Discovery: As applications shift to microservices, ASM tools are specializing in finding unauthenticated or “zombie” APIs that provide backdoors to databases.
- Governance of Third-Party Assets: Organizations are increasingly using ASM to monitor the security posture of their critical vendors and supply chain partners.
- Red Team Automation: ASM platforms are integrating automated “breach and attack” simulations to test if a discovered vulnerability is actually reachable and exploitable.
- Focus on Digital Sovereignty: Tools are adding features to help companies identify assets hosted in specific geographical regions to comply with strict data residency laws.
- Consolidation of Point Solutions: ASM capabilities are being swallowed by larger XDR (Extended Detection and Response) and Vulnerability Management suites to provide a unified risk view.
How We Selected These Tools (Methodology)
To determine the leading Attack Surface Management solutions, we conducted a technical assessment focused on the operational needs of modern security operations centers (SOCs). Our methodology included:
- Discovery Breadth: We prioritized tools that scan not just IP addresses, but also DNS records, social media, and dark web forums.
- Attribution Logic: We evaluated the sophistication of the algorithms used to link “stray” assets to a specific corporate identity.
- Signal-to-Noise Ratio: We favored tools that prioritize “high-fidelity” alerts over massive lists of low-risk or irrelevant data.
- Integration Flexibility: We looked for platforms with robust APIs that can feed data into Jira, ServiceNow, or Splunk.
- Market Reliability: We selected vendors with a proven track record of supporting large-scale enterprise environments.
- Speed to Insight: We analyzed how quickly each tool moves from initial “seed” entry to a comprehensive map of the attack surface.
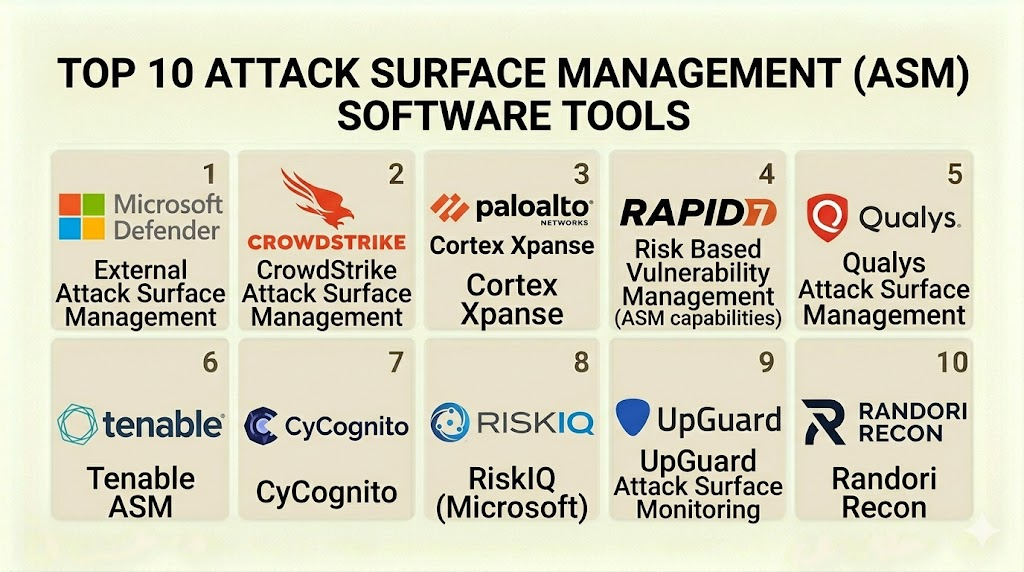
Top 10 Attack Surface Management (ASM) Software Tools
#1 — Palo Alto Networks Cortex Xpanse
Short description: A premier, enterprise-grade ASM platform that provides a complete, outside-in view of an organization’s global internet-facing assets and risks.
Key Features
- Active Discovery: Continuously indexes the entire internet to find assets that belong to your organization.
- Policy Enforcement: Automatically identifies assets that violate corporate security policies (e.g., telnet open to the web).
- Automated Remediation: Integrates with Cortex XSOAR to trigger automatic playbooks when new risks are found.
- Service Attribution: Uses advanced algorithms to map services to specific business units or subsidiaries.
- Cloud Governance: Identifies “unmanaged” cloud instances that are not protected by standard security agents.
- RDP/VPN Detection: Specifically monitors for exposed remote access points that are frequent targets for ransomware.
Pros
- Offers one of the most comprehensive and high-fidelity discovery databases in the world.
- Deeply integrates with the broader Palo Alto Networks security ecosystem.
Cons
- Premium pricing that is generally geared toward large enterprise budgets.
- Initial setup and tuning of attribution can require dedicated security expertise.
Platforms / Deployment
- SaaS / Cloud
- Global Deployment
Security & Compliance
- SSO/SAML, MFA, RBAC.
- SOC 2 Type II, ISO 27001.
Integrations & Ecosystem
Designed to be the center of a modern SOC, it offers native hooks into major security tools.
- Cortex XSOAR
- Splunk
- ServiceNow
- AWS / Azure / GCP
Support & Community
Industry-leading enterprise support with 24/7 technical assistance and a robust user community through the Palo Alto Networks LIVEcommunity.
#2 — CyCognito
Short description: A platform designed to uncover the path of least resistance for attackers by identifying the most critical risks across the entire digital ecosystem.
Key Features
- Path of Least Resistance Analysis: Ranks risks based on how easily an attacker could exploit them to reach sensitive data.
- Full Context Discovery: Provides details on why an asset exists, who owns it, and what data it might be accessing.
- Evidence-Based Testing: Performs safe, automated testing on discovered assets to confirm if vulnerabilities are actually exploitable.
- Subsidiary Mapping: Automatically discovers the attack surfaces of acquisitions and partners.
- Risk Scoring: Assigns grades to different business units to help executives understand where security is lagging.
- Remediation Guidance: Provides step-by-step instructions for IT teams to close discovered gaps.
Pros
- Exceptional at prioritizing “business risk” rather than just providing a list of CVEs.
- Highly automated discovery requires very little “seed” information to start.
Cons
- Can be overwhelming for smaller teams without a dedicated remediation process.
- The high level of detail can occasionally lead to complex reporting that needs simplification for executives.
Platforms / Deployment
- SaaS
- Cloud-Native
Security & Compliance
- MFA, SSO, Data Encryption.
- SOC 2.
Integrations & Ecosystem
Built to feed remediation workflows in enterprise environments.
- Jira
- ServiceNow
- Slack
- Tenable / Qualys
Support & Community
Excellent customer success programs and a growing library of technical documentation and webinars.
#3 — Microsoft Defender External Attack Surface Management (EASM)
Short description: Built on technology acquired from RiskIQ, this tool provides a comprehensive map of the digital footprint and the associated risks.
Key Features
- Unmanaged Asset Discovery: Finds assets that are not currently under the management of Azure or other Microsoft tools.
- Continuous Monitoring: Scans for changes in the attack surface every 24 hours.
- Vulnerability Mapping: Correlates discovered assets with known vulnerabilities and exposures.
- Certificate Management: Identifies expiring or weak SSL/TLS certificates across the entire estate.
- Dashboard Integration: Native integration with the Microsoft Defender for Cloud portal.
- Snapshot Views: Provides historical data to see how the attack surface has evolved over time.
Pros
- Ideal for organizations already committed to the Microsoft Azure and 365 ecosystems.
- Leverages the massive threat intelligence data gathered by Microsoft globally.
Cons
- Discovery capabilities are strongest within the Microsoft ecosystem compared to niche competitors.
- Reporting can feel fragmented across different Microsoft security portals.
Platforms / Deployment
- SaaS / Azure Integrated
- Cloud
Security & Compliance
- Azure AD / Entra ID, RBAC.
- ISO 27001, SOC 1/2/3, HIPAA, FedRAMP.
Integrations & Ecosystem
Designed to be a part of the unified Microsoft security stack.
- Microsoft Sentinel
- Defender for Cloud
- Azure DevOps
- Logic Apps
Support & Community
Supported by Microsoft’s global enterprise support infrastructure and the vast Microsoft Technical Community.
#4 — Tenable.asm
Short description: An extension of the Tenable vulnerability management platform that provides visibility into the external-facing assets and their risks.
Key Features
- Comprehensive Inventory: Identifies all internet-facing assets including domains, subdomains, and IP addresses.
- Subsidiary Discovery: Allows parent companies to see the attack surface of all their sub-organizations.
- Change Detection: Alerts security teams when a new asset appears or an old one changes configuration.
- Risk Prioritization: Uses Tenable’s Vulnerability Priority Rating (VPR) to focus on the most dangerous flaws.
- Cloud Instance Mapping: Finds unmanaged cloud assets across all major providers.
- Technology Profiling: Identifies the software stack running on discovered assets (e.g., specific versions of Apache).
Pros
- Perfect for existing Tenable.io users who want a unified view of internal and external risks.
- Strong focus on technical accuracy and reduced false positives.
Cons
- The interface can be complex for users who are not already familiar with Tenable’s logic.
- Requires a Tenable.io or Tenable.one subscription for full feature access.
Platforms / Deployment
- SaaS
- Cloud
Security & Compliance
- SSO, MFA, Encryption at rest and in transit.
- SOC 2, ISO 27001.
Integrations & Ecosystem
Integrates deeply with Tenable’s wider vulnerability management tools.
- Tenable.io / Tenable.sc
- Jira
- ServiceNow
- AWS / Azure
Support & Community
Backed by Tenable’s mature professional services and the “Tenable Community” knowledge base.
#5 — Mandiant Advantage Attack Surface Management
Short description: A platform that combines automated discovery with Mandiant’s world-class threat intelligence to provide a defender’s view of the attack surface.
Key Features
- Intelligence-Led Discovery: Focuses on the assets and vulnerabilities that Mandiant knows are being targeted by state-sponsored actors.
- Asset Attribution: Highly accurate mapping of assets back to the parent organization.
- Continuous Exposure Monitoring: Constant scanning for new open ports, misconfigured services, and leaked data.
- Dashboards for Executives: High-level views that translate technical risk into business impact.
- Active Monitoring: Alerts on changes to DNS, WHOIS, and SSL certificate records.
- Integration with Threat Intelligence: Directly links discovered assets to known APT (Advanced Persistent Threat) group behaviors.
Pros
- Provides arguably the best threat-context in the industry due to Mandiant’s frontline experience.
- Excellent for high-security organizations that are frequent targets of sophisticated attacks.
Cons
- The focus on high-level intelligence can be “too much” for smaller, less-targeted companies.
- Now part of Google Cloud, which may influence future integration directions.
Platforms / Deployment
- SaaS
- Cloud
Security & Compliance
- Standard Google Cloud security protocols, SSO, RBAC.
- SOC 2, ISO 27001.
Integrations & Ecosystem
Expanding its footprint within the Google Cloud security ecosystem.
- Google Chronicle
- Sentinel / Splunk
- ServiceNow
- Mandiant Threat Intelligence
Support & Community
Professional support from Mandiant’s incident response and security consulting teams.
#6 — Randori (An IBM Company)
Short description: A platform that focuses on “Attacker’s Intent,” helping teams prioritize assets based on how attractive they are to a real-world adversary.
Key Features
- Target Temptation: A unique scoring system that ranks assets by how likely an attacker is to target them.
- Automated Discovery: Continuously maps the external perimeter with minimal input.
- Black Box Perspective: Views the organization exactly as an outsider would, finding forgotten entry points.
- Vulnerability Research: Includes proprietary research on zero-day and n-day vulnerabilities.
- Remediation Prioritization: Focuses on the “entry points” rather than just a long list of bugs.
- Impact Analysis: Shows what an attacker could potentially access if they breached a specific discovered asset.
Pros
- The “Target Temptation” logic is highly effective for focused remediation.
- Simplified interface that is easier to navigate than many traditional security tools.
Cons
- May lack the sheer volume of discovery features found in platforms like Xpanse.
- Integration with non-IBM tools is growing but still maturing.
Platforms / Deployment
- SaaS
- Cloud
Security & Compliance
- IBM Cloud security standards, SSO, MFA.
- SOC 2, HIPAA.
Integrations & Ecosystem
Deepening integration with the IBM Security QRadar and Resilient platforms.
- IBM QRadar
- IBM Resilient (SOAR)
- Jira
- Splunk
Support & Community
Supported by IBM’s global enterprise support and the Randori customer success team.
#7 — Censys Attack Surface Management
Short description: Built on top of the world’s most comprehensive internet scan data, Censys provides a high-fidelity map of every global asset.
Key Features
- Internet-Wide Scanning: Uses its proprietary data engine to provide real-time views of the entire internet.
- Automatic Inventory: Finds subdomains, certificates, and IP addresses using a single domain as a seed.
- Risk Identification: Flags high-risk exposures such as expired certificates and exposed databases.
- Historical Data: Allows users to travel back in time to see when an asset first appeared or changed.
- Cloud Discovery: Specifically identifies resources in “unclaimed” cloud accounts.
- API-First Approach: Extremely robust API for custom security automation and integration.
Pros
- The data quality is exceptionally high, as many other ASM tools actually buy data from Censys.
- Very fast discovery times compared to many traditional scanners.
Cons
- Requires a more technical user to get the most out of the data and API.
- Reporting is very functional but less “executive-ready” than some competitors.
Platforms / Deployment
- SaaS
- Cloud-Based Data
Security & Compliance
- MFA, SSO, RBAC.
- SOC 2 Type II.
Integrations & Ecosystem
Excellent for teams that build their own security workflows.
- Splunk
- Tenable
- Qualys
- Rapid7
Support & Community
Dedicated technical support and a large community of researchers who use Censys data.
#8 — Rapid7 InsightCloudSec (with ASM)
Short description: A unified platform that combines Cloud Security Posture Management (CSPM) with Attack Surface Management to protect the modern perimeter.
Key Features
- Continuous Discovery: Identifies and monitors internet-facing cloud and on-prem assets.
- Unified Visibility: Combines external ASM data with internal cloud configuration data.
- Real-Time Risk Scoring: Prioritizes assets based on both external exposure and internal importance.
- Automation Hooks: Triggers automated remediation within the Insight platform.
- Shadow IT Detection: Finds cloud assets that are not governed by central IT policies.
- Compliance Mapping: Maps discovered risks to frameworks like CIS and NIST.
Pros
- Strong choice for organizations that need to secure complex, multi-cloud environments.
- Benefit of being part of the Rapid7 Insight platform for unified vulnerability management.
Cons
- ASM features are most effective when purchased as part of the larger InsightCloudSec suite.
- Can be resource-heavy during the initial configuration phase.
Platforms / Deployment
- SaaS
- Cloud-Native
Security & Compliance
- SSO, MFA, Advanced Encryption.
- SOC 2, ISO 27001, HIPAA.
Integrations & Ecosystem
Integrates with the full Rapid7 security portfolio.
- InsightIDR
- InsightVM
- Jira
- ServiceNow
Support & Community
Professional support through Rapid7 and the active “Rapid7 Customer Community” forum.
#9 — Bugcrowd Attack Surface Management
Short description: A unique approach that combines automated scanning with human intelligence from a global community of security researchers.
Key Features
- Asset Discovery: Automated tools to map the digital footprint.
- Human-in-the-Loop: Uses researchers to verify and attribute assets, reducing false positives.
- Prioritized Remediation: Focuses on the assets that researchers find most “attractive” for testing.
- Seamless Transition to Bug Bounty: Easily moves discovered assets into a vulnerability disclosure program.
- Vulnerability Attribution: Proves the ownership of assets using researcher-validated evidence.
- Executive Dashboards: Shows the reduction in attack surface over time through researcher activity.
Pros
- Significantly lower false positive rate due to human verification.
- Excellent for teams that want to bridge ASM with crowdsourced security testing.
Cons
- The human-verification aspect can take slightly longer than pure machine-based tools.
- Costs can be variable depending on the level of researcher engagement.
Platforms / Deployment
- SaaS
- Managed / Crowdsourced
Security & Compliance
- Standard SaaS security, SSO.
- SOC 2.
Integrations & Ecosystem
Designed to feed vulnerability and asset data into development workflows.
- Jira
- GitHub
- Azure DevOps
- Slack
Support & Community
Access to a massive community of over 100,000 security researchers and Bugcrowd’s internal success team.
#10 — SpiderFoot (Open Source / Elite)
Short description: A highly popular, flexible tool used by security researchers and small teams to automate OSINT (Open Source Intelligence) and ASM.
Key Features
- Over 200 Data Sources: Pulls information from WHOIS, DNS, social media, and leaked databases.
- Automated OSINT: Automates the gathering of intelligence on domains, IPs, and email addresses.
- Modular Architecture: Allows users to enable or disable specific discovery modules as needed.
- Visual Mapping: Provides a node-based graph of how discovered assets are connected.
- Self-Hosted or Cloud: Offers a free open-source version and a managed “Elite” version for enterprises.
- Target Monitoring: Can be set to alert when specific new data is found regarding a target.
Pros
- The open-source version is the most powerful free tool for basic ASM discovery.
- Incredible depth of data source integrations for advanced researchers.
Cons
- Requires a high level of technical skill to configure and interpret results.
- Can generate a very high amount of “noise” if not tuned correctly.
Platforms / Deployment
- Linux / macOS / Windows / SaaS
- Self-hosted / Cloud
Security & Compliance
- Self-managed for Open Source; Standard SaaS for Elite.
- N/A (Open Source).
Integrations & Ecosystem
Highly extensible through its modular Python-based architecture.
- Shodan / Censys / BinaryEdge
- VirusTotal
- Have I Been Pwned
- Slack
Support & Community
Massive community support via GitHub and a professional support tier for “Elite” subscribers.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| Cortex Xpanse | Global Enterprise | Windows, Linux, Mac | SaaS | Internet-wide active scan | 4.8/5 |
| CyCognito | Business Risk Focus | Cloud Native | SaaS | Path of Least Resistance | 4.7/5 |
| Microsoft Defender | Microsoft Ecosystem | Azure / Cloud | SaaS | Native Sentinel Sync | 4.5/5 |
| Tenable.asm | Unified VM Teams | Cloud | SaaS | Tenable VPR Integration | 4.4/5 |
| Mandiant ASM | Targeted Intelligence | Cloud | SaaS | APT-focused Discovery | 4.6/5 |
| Randori | Attacker Perspective | Cloud | SaaS | Target Temptation Score | 4.5/5 |
| Censys ASM | Data Quality / APIs | Cloud | SaaS | Proprietary Data Engine | 4.8/5 |
| InsightCloudSec | Multi-Cloud Teams | Cloud Native | SaaS | CSPM + ASM Unified | 4.3/5 |
| Bugcrowd ASM | Human Verification | Managed / SaaS | SaaS | Crowdsourced Validation | 4.7/5 |
| SpiderFoot | Researchers / OSINT | All OS / SaaS | Self-hosted | 200+ Module Integration | 4.6/5 |
Evaluation & Scoring of Attack Surface Management (ASM)
To determine the effectiveness of an ASM tool, organizations should use a weighted scoring model. This ensures that the platform aligns with specific infrastructure needs and technical capabilities.
| Tool Name | Discovery (25%) | Attribution (15%) | Integrations (15%) | Security (10%) | Monitoring (10%) | Support (10%) | Value (15%) | Weighted Total |
| Xpanse | 10 | 9 | 10 | 9 | 10 | 9 | 6 | 8.85 |
| CyCognito | 9 | 9 | 8 | 9 | 9 | 9 | 7 | 8.50 |
| Microsoft | 8 | 8 | 10 | 10 | 8 | 9 | 8 | 8.55 |
| Tenable | 8 | 8 | 9 | 9 | 8 | 9 | 8 | 8.30 |
| Mandiant | 9 | 9 | 8 | 9 | 9 | 9 | 7 | 8.50 |
| Randori | 8 | 8 | 8 | 9 | 8 | 8 | 8 | 7.95 |
| Censys | 10 | 7 | 9 | 8 | 9 | 8 | 8 | 8.40 |
| Rapid7 | 7 | 7 | 9 | 9 | 8 | 8 | 8 | 7.75 |
| Bugcrowd | 8 | 10 | 7 | 9 | 7 | 9 | 7 | 7.85 |
| SpiderFoot | 9 | 6 | 7 | 5 | 7 | 6 | 10 | 7.40 |
Scoring Logic:
- Discovery (25%): The ability to find assets across all layers of the internet.
- Attribution (15%): The accuracy in proving an asset belongs to the user.
- Integrations (15%): How well it feeds into the existing security stack.
- Weighted Total: Calculated on a 0-10 scale. A score above 8.0 represents an industry-leading enterprise solution.
Which Attack Surface Management (ASM) Tool Is Right for You?
Solo / Freelancer
For an individual researcher or a consultant, SpiderFoot is the best starting point. The open-source version allows for deep investigative work without the high cost of enterprise licenses. It is excellent for “point-in-time” assessments of small digital footprints.
SMB
Small and medium businesses that need to protect a growing cloud presence should look at Censys ASM or Tenable.asm. These tools provide high-quality data and easy-to-use interfaces that don’t require a dedicated 24/7 SOC team to manage.
Mid-Market
Organizations that are already integrated into major ecosystems like Microsoft or Rapid7 should start with their native offerings (Microsoft Defender EASM or InsightCloudSec). This reduces the “tool fatigue” and allows for a unified dashboard for both internal and external risks.
Enterprise
For large, global organizations, Palo Alto Networks Cortex Xpanse or CyCognito are the clear choices. These platforms are built to handle hundreds of thousands of assets and provide the automated remediation and risk-prioritization logic needed to manage enterprise-scale complexity.
Budget vs Premium
- Budget: SpiderFoot (Open Source), AWS WAF (Basic rules), Censys (Startup tiers).
- Premium: Cortex Xpanse, Mandiant Advantage, CyCognito.
Feature Depth vs Ease of Use
- Maximum Depth: Cortex Xpanse, Censys ASM.
- Ease of Use: Microsoft Defender EASM, Randori.
Integrations & Scalability
- Best for Scaling: Cortex Xpanse, Microsoft Defender.
- Best for Integrations: Tenable.asm, Rapid7.
Security & Compliance Needs
Organizations in highly regulated sectors like Finance or Government should prioritize Microsoft Defender or Mandiant Advantage, as they carry the most extensive government-level certifications and handle data within strict sovereign boundaries.
Frequently Asked Questions (FAQs)
1. What is the difference between ASM and Vulnerability Management?
Vulnerability Management typically focuses on patching known software bugs on assets you already know you have. ASM focuses on finding the assets you didn’t know you had, so that you can then bring them into your vulnerability management program.
2. Can ASM tools find assets in the dark web?
Some advanced ASM tools like Mandiant or Cortex Xpanse can scan dark web forums and leaked databases to find mentions of your corporate credentials, IP ranges, or stolen source code that may indicate an exposed attack surface.
3. Do I need an agent to use Attack Surface Management tools?
No, one of the primary benefits of ASM is that it is “agentless.” Because it looks at your organization from the perspective of an external attacker, it only requires your domain name or known IP ranges to begin discovery.
4. How often should an ASM tool scan my attack surface?
In a modern environment where cloud instances can be spun up in seconds, scans should be continuous or at least daily. Most top-tier tools scan the entire internet multiple times a day to identify changes in real-time.
5. Does ASM replace traditional penetration testing?
No, ASM and penetration testing are complementary. ASM provides a continuous, high-level map of your perimeter, while penetration testing is a deep, point-in-time human-led exercise to find complex logic flaws.
6. What is “Shadow IT” in the context of ASM?
Shadow IT refers to any application, server, or cloud service used by employees without the explicit approval or knowledge of the IT department. ASM tools are the most effective way to find these “hidden” risks.
7. How do ASM tools avoid blocking or scanning the wrong companies?
ASM tools use “Attribution” logic, which looks at SSL certificate signatures, DNS history, and WHOIS data to verify that an asset truly belongs to your organization before adding it to your risk dashboard.
8. Can ASM help with merger and acquisition (M&A) due diligence?
Yes, ASM is a vital tool for M&A. It allows the acquiring company to see the full digital risk profile of a target company before the deal is finalized, identifying hidden debts and security liabilities.
9. What is an “Attacker’s Eye View”?
An “Attacker’s Eye View” means looking at your digital infrastructure without any insider knowledge. It means finding what is actually exposed and reachable, rather than what you believe is exposed based on your internal documentation.
10. Are ASM tools compliant with global privacy laws like GDPR?
Most reputable ASM tools only collect publicly available internet data (OSINT). As long as they are not scraping private personal data without consent, they generally comply with privacy regulations focused on corporate security data.
Conclusion
Attack Surface Management is no longer a luxury for the security-conscious; it is a fundamental pillar of modern cybersecurity. As organizations continue to move toward the cloud and adopt decentralized work models, the “perimeter” will only become more fragmented. The ability to see exactly what an attacker sees—and to close those gaps before they are exploited—is the only way to maintain a resilient defense.Whether you choose the massive scanning power of Cortex Xpanse, the risk-based intelligence of Mandiant, or the accessibility of Microsoft Defender, the goal is clear: total visibility. By choosing a tool that fits your scale and integration needs, you can turn your “dark” digital assets into a well-lit, managed, and secured part of your enterprise.