Find the Best Cosmetic Hospitals — Choose with Confidence
Discover top cosmetic hospitals in one place and take the next step toward the look you’ve been dreaming of.
“Your confidence is your power — invest in yourself, and let your best self shine.”
Compare • Shortlist • Decide smarter — works great on mobile too.
Introduction
Network Detection and Response (NDR) is a category of cybersecurity solutions that provide deep visibility into internal network traffic to identify, investigate, and mitigate malicious activities. While traditional firewalls focus on the perimeter and Endpoint Detection and Response (EDR) focuses on individual devices, NDR monitors the “east-west” traffic—the movement of data between servers and users within the network. It functions by analyzing raw network packets or traffic metadata (like NetFlow) to establish a baseline of normal behavior. When deviations occur, such as a sudden data exfiltration attempt or lateral movement by an attacker, the NDR system triggers an alert or automated response.
In the modern threat landscape, NDR has become a non-negotiable layer of the security stack. As attackers become more adept at bypassing perimeter defenses and living off the land, the network becomes the ultimate source of truth. NDR platforms leverage advanced machine learning and behavioral analytics to find “quiet” threats that do not use known malware signatures. By providing a continuous, high-fidelity view of network interactions, these tools enable security teams to stop breaches before they escalate into full-scale data disasters.
Real-world use cases:
- Lateral Movement Detection: Identifying when an attacker has gained a foothold on one machine and is attempting to move to a high-value database.
- Encrypted Threat Analysis: Detecting malware patterns or command-and-control (C2) communication within encrypted traffic without requiring full decryption.
- Insider Threat Monitoring: Spotting unusual data access patterns from a legitimate employee account that might indicate credential theft or malicious intent.
- Cloud and Hybrid Visibility: Monitoring traffic across on-premises data centers and public cloud environments to ensure consistent security policy.
- Incident Investigation: Providing a forensic “tape recorder” of network events to help analysts reconstruct exactly how a breach occurred.
Evaluation criteria for buyers:
- Detection Accuracy: The ability to find sophisticated threats with a low rate of false positives.
- Traffic Coverage: Support for diverse environments, including physical networks, virtualized data centers, and public clouds.
- Response Capabilities: Options for automated blocking, session termination, or integration with SOAR platforms.
- Encrypted Traffic Analysis (ETA): The capability to analyze encrypted packets for risk without compromising privacy or performance.
- Deployment Flexibility: Availability as a physical appliance, virtual sensor, or cloud-native agent.
- Integration Ecosystem: How well the tool shares data with EDR, SIEM, and identity providers.
- Historical Forensics: The depth and duration of network metadata storage for investigative purposes.
- Ease of Use: The intuitiveness of the dashboard and the clarity of threat alerts.
- Scalability: The ability to process gigabits or terabits of data per second without dropping packets.
- Total Cost of Ownership: Licensing fees, hardware requirements, and the human resources needed to manage the tool.
Mandatory Paragraph
- Best for: Large enterprises, financial institutions, government agencies, and organizations with high-value intellectual property that require deep visibility into internal network movements to combat advanced persistent threats (APTs).
- Not ideal for: Very small businesses with a single-site office and no sensitive data, or organizations that rely entirely on SaaS applications without any managed infrastructure.
Key Trends in Network Detection & Response
- AI-Driven Autonomous Response: NDR platforms are moving toward self-healing networks where AI can instantly quarantine a suspicious host without waiting for human approval.
- Unified XDR Integration: NDR is increasingly being absorbed into Extended Detection and Response (XDR) frameworks, providing the network context to endpoint and identity data.
- SaaS-Based Management: Even for on-premises monitoring, management consoles are shifting to the cloud to allow for global visibility and easier updates.
- Decentralized Sensors: The rise of remote work is driving the deployment of lightweight sensors on remote gateways and cloud edges to capture traffic outside the traditional HQ.
- Focus on OT/IoT Security: NDR tools are expanding their protocol support to detect threats in specialized Operational Technology (OT) and industrial environments.
- Advanced Decryption Offloading: Strategic use of hardware acceleration to decrypt and inspect high-priority traffic without slowing down the core network.
- Zero Trust Enforcement: NDR acts as the “referee” for Zero Trust architectures, verifying that network flows match the intended micro-segmentation policies.
- Threat Intelligence Fusion: Real-time ingestion of global threat feeds to automatically tag network events with known attacker group signatures.
How We Selected These Tools (Methodology)
To identify the leading NDR solutions, we followed a rigorous methodology focused on operational efficacy and enterprise reliability:
- Market mindshare: Prioritizing tools recognized by major industry analysts and widely adopted by the Global 2000.
- Feature maturity: Evaluating the sophistication of the machine learning models and the depth of the response playbooks.
- Interoperability: Focusing on tools that offer open APIs and pre-built connectors for a “best-of-breed” security stack.
- Security signals: Analyzing the vendor’s own security posture and commitment to data privacy and encryption standards.
- Scalability: Ensuring the selected tools can handle the massive throughput requirements of modern data centers.
- Customer feedback: Reviewing signals of reliability and performance from existing users in complex environments.
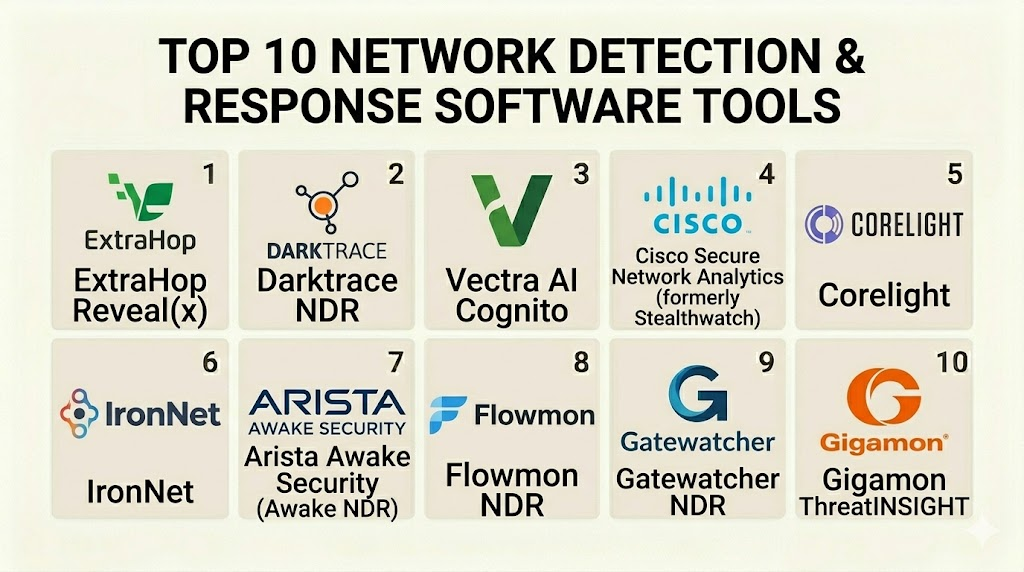
Top 10 Network Detection & Response Software Tools
1 — Darktrace
Short description: Darktrace is a pioneer in “Self-Learning AI” for cybersecurity. It learns a “pattern of life” for every user and device on the network to detect subtle anomalies that indicate a breach.
Key Features
- Enterprise Immune System: Uses unsupervised machine learning to establish a baseline of normal network behavior.
- Antigena Response: An autonomous response module that can surgically block connections in real-time.
- Cyber AI Analyst: Automatically investigates alerts to present a cohesive narrative of the threat.
- Cloud and SaaS Coverage: Extends visibility into environments like AWS, Azure, and Microsoft 365.
- Encrypted Traffic Analysis: Identifies risks in encrypted flows without requiring decryption.
- Email Integration: Correlates network behavior with email threats for a multi-vector view.
Pros
- Requires zero prior knowledge of threats or signatures to be effective.
- Autonomous response significantly reduces the “mean time to respond” (MTTR).
Cons
- Can produce a high volume of alerts during the initial learning phase.
- The premium pricing model may be out of reach for mid-sized organizations.
Platforms / Deployment
- Windows / macOS / Linux / Cloud
- Physical appliance / Virtual / Cloud / Hybrid
Security & Compliance
- SSO/SAML, RBAC, Data encryption at rest.
- ISO 27001, SOC 2, GDPR.
Integrations & Ecosystem
Darktrace integrates with a wide variety of security tools to share insights and trigger responses.
- Splunk and Sentinel
- CrowdStrike and Carbon Black
- Okta and Active Directory
- ServiceNow
Support & Community
Darktrace offers 24/7 technical support, a dedicated customer success manager, and a comprehensive online portal with training and documentation.
2 — Vectra AI
Short description: Vectra AI focuses on identifying attacker behaviors rather than just anomalies. Its platform, Cognito, tracks the progression of an attack from reconnaissance to exfiltration.
Key Features
- Cognito Detect: Automatically identifies hidden attackers by analyzing metadata from all network traffic.
- Cognito Recall: Provides a long-term storage solution for network metadata to support forensic investigations.
- AI-Assisted Triage: Prioritizes alerts based on the potential risk to critical assets.
- Privileged Identity Analytics: Monitors the use of administrative accounts to find credential abuse.
- Native Cloud Support: Built-in visibility for IaaS and PaaS workloads.
- Custom Playbooks: Allows teams to define specific automated actions for different threat types.
Pros
- High efficiency in finding lateral movement and data exfiltration.
- Reduces analyst burnout by condensing thousands of events into a few actionable incidents.
Cons
- Metadata-only approach may lack the depth of full packet capture for some forensic needs.
- The initial configuration of “critical assets” is vital for accurate scoring.
Platforms / Deployment
- Web / Cloud / Windows / Linux
- Cloud / Virtual / Hybrid
Security & Compliance
- MFA, SSO, RBAC.
- Not publicly stated.
Integrations & Ecosystem
Vectra AI is built to be the “analytical engine” that feeds into a broader security ecosystem.
- Microsoft Defender and Sentinel
- Amazon GuardDuty
- Cisco ISE
- Splunk
Support & Community
Vectra offers robust professional services, a community forum for threat hunters, and standard enterprise support tiers.
3 — ExtraHop Reveal(x)
Short description: ExtraHop Reveal(x) uses cloud-native NDR to provide complete visibility and real-time threat detection across the entire hybrid enterprise.
Key Features
- Line-Rate Decryption: Decrypts traffic (including TLS 1.3) at massive scale to find hidden malware.
- Asset Discovery: Automatically identifies and classifies every device on the network.
- Cloud-Native Design: Offers native integration with cloud flow logs and VPC mirroring.
- Behavioral Models: Uses over 5,000 architectural features to identify anomalies.
- One-Click Response: Integrated actions for Palo Alto and CrowdStrike to isolate hosts.
- Guided Investigation: Directs analysts through the “next steps” for any given alert.
Pros
- Superior performance in high-throughput environments (up to 100 Gbps).
- Deep decryption capabilities provide insights that metadata-only tools miss.
Cons
- High hardware requirements for on-premises packet processing.
- Can be complex to tune for very noisy environments.
Platforms / Deployment
- Web / Windows / macOS / Linux
- Cloud / Physical appliance / Virtual
Security & Compliance
- SSO, Encryption, RBAC.
- SOC 2 Type II, HIPAA, GDPR.
Integrations & Ecosystem
ExtraHop excels at “wire data” integration, feeding high-fidelity data into other tools.
- Palo Alto Networks
- CrowdStrike
- Splunk and IBM QRadar
- AWS and Azure
Support & Community
ExtraHop provides 24/7 global support, an extensive training academy, and a popular community Slack channel for users.
4 — Cisco Secure Network Analytics
Short description: Formerly known as Stealthwatch, this platform is a veteran in the NDR space, utilizing NetFlow and Telemetry to provide scalable visibility.
Key Features
- Flow-Based Monitoring: Analyzes NetFlow, IPFIX, and other telemetry from existing network infrastructure.
- Encrypted Analytics: Uses Cisco’s Encrypted Traffic Analytics (ETA) to find threats without decryption.
- Cisco ISE Integration: Allows for automated quarantine using Identity Services Engine.
- Cognitive Threat Analytics: A cloud-based engine that finds command-and-control activity.
- Multicloud Visibility: Monitors traffic in AWS, Azure, and Google Cloud.
- Entity Modeling: Builds a behavior profile for every device to spot deviations.
Pros
- Scales easily across massive global networks using existing routers and switches.
- Highly cost-effective if you already have a Cisco-heavy infrastructure.
Cons
- Relies heavily on telemetry which may not be as granular as full packet inspection.
- Interface can feel dated compared to newer, cloud-native startups.
Platforms / Deployment
- Windows / Linux / Web
- Physical appliance / Virtual / Cloud / Hybrid
Security & Compliance
- MFA, SSO, RBAC.
- Not publicly stated.
Integrations & Ecosystem
Deeply integrated into the Cisco “SecureX” architecture.
- Cisco ISE and Firepower
- Splunk
- ServiceNow
- SecureX platform
Support & Community
Backed by Cisco TAC, one of the most comprehensive support organizations in the IT industry.
5 — Corelight
Short description: Corelight is the commercial provider of Zeek (formerly Bro), providing open-source-based network telemetry with enterprise-grade management.
Key Features
- Zeek-Powered: Leverages the world’s most popular open-source network security monitoring framework.
- Smart PCAP: Captures only the packets related to suspicious activity to save on storage.
- Corelight Sensors: Purpose-built hardware or virtual sensors designed for high-speed traffic.
- Encrypted Traffic Insights: Extracts metadata from encrypted flows to find certificates and JA3 fingerprints.
- Cloud Sensors: Specialized versions for AWS, Azure, and Google Cloud traffic mirroring.
- Open Data Export: Sends data in a clean format to SIEMs or data lakes for custom analysis.
Pros
- High flexibility; allows security teams to write custom scripts to find unique threats.
- The most transparent and “open” NDR platform on the market.
Cons
- Requires a higher level of technical skill to manage and interpret Zeek data.
- Focuses more on “Detection” and “Evidence” than automated “Response.”
Platforms / Deployment
- Linux / Windows / macOS / Web
- Physical appliance / Virtual / Cloud
Security & Compliance
- RBAC, Encryption, SSO.
- Not publicly stated.
Integrations & Ecosystem
Corelight is designed to be the “data source” for the modern SOC.
- Splunk and Humio
- CrowdStrike
- Microsoft Sentinel
- Elastic Stack
Support & Community
Corelight provides 24/7 support and is a major contributor to the massive Zeek open-source community.
6 — Arista Awake Security
Short description: Arista’s NDR platform uses an entity-centric approach, tracking every device and user over time to find advanced attackers.
Key Features
- Ava AI: An autonomous virtual assistant that automates threat hunting and triage.
- Entity Tracking: Tracks assets by fingerprint, not just IP, to maintain visibility as they move.
- Encrypted Analysis: Analyzes packet headers and timing to find threats in HTTPS traffic.
- Adversarial Modeling: Uses a specialized language to search for specific attacker techniques.
- Full Packet Forensics: Provides deep access to raw traffic for the highest level of investigation.
- IoT Visibility: Specifically identifies and monitors unmanaged IoT and medical devices.
Pros
- Excellent at identifying “headless” devices like printers and smart building systems.
- Reduced false positives through high-context entity modeling.
Cons
- Can be hardware-intensive for full packet capture at high speeds.
- The advanced query language has a learning curve for new analysts.
Platforms / Deployment
- Web / Windows / Linux
- Physical appliance / Virtual / Cloud
Security & Compliance
- MFA, RBAC, SSO.
- SOC 2.
Integrations & Ecosystem
Arista NDR works well within the campus and data center networking fabric.
- Palo Alto Networks
- CrowdStrike
- SentinelOne
- Splunk
Support & Community
Standard enterprise support, plus professional threat hunting services offered by Arista experts.
7 — Fidelis Network
Short description: Fidelis provides a holistic NDR platform that focuses on automated detection and response across network and cloud environments.
Key Features
- Deep Session Inspection: Analyzes all 65,535 ports to find data leakage and threats.
- Automated Response: Triggers scripts and playbooks to stop data theft automatically.
- Asset Discovery: Maps your entire digital terrain, including shadow IT and cloud.
- Metadata Storage: Keeps high-fidelity records of every transaction for months.
- Decryption Support: Native SSL/TLS decryption for deeper content inspection.
- Malware Analysis: Integrated sandbox to analyze files found in transit.
Pros
- Strong focus on Data Loss Prevention (DLP) alongside threat detection.
- Comprehensive visibility into “all ports and protocols,” not just web traffic.
Cons
- The management console can be complex due to the high density of data.
- On-premises deployments can require significant administrative overhead.
Platforms / Deployment
- Windows / Linux / Web
- Physical appliance / Virtual / Cloud / Hybrid
Security & Compliance
- SSO, RBAC, Encryption.
- Not publicly stated.
Integrations & Ecosystem
Fidelis is often used as a central piece of a multi-platform security strategy.
- Fidelis Endpoint and Deception
- Splunk
- McAfee
- ServiceNow
Support & Community
Fidelis offers 24/7 support, dedicated training, and “managed detection and response” (MDR) services.
8 — IronNet IronDefense
Short description: IronNet stands out with its “Collective Defense” model, allowing organizations to share threat intelligence in real-time.
Key Features
- Collective Defense: Shares anonymized threat insights with other IronNet customers in your industry.
- Behavioral Analytics: Uses ML to find anomalies in DNS, HTTP, and other common protocols.
- IronDome: A community platform for real-time peer-to-peer threat information sharing.
- Expert Triage: Alerts are reviewed by IronNet’s SOC before being sent to the customer.
- Cloud Native Integration: Native visibility for AWS and Azure environments.
- Network Mapping: Visualizes how traffic flows between different segments of your network.
Pros
- Provides a “neighborhood watch” effect that helps companies prepare for industry-specific attacks.
- Highly effective for critical infrastructure and defense-related sectors.
Cons
- Requires a “community” approach which may not suit companies with extreme privacy silos.
- The core engine is less focused on “Response” than some competitors.
Platforms / Deployment
- Windows / Linux / Web
- Cloud / Virtual / Hybrid
Security & Compliance
- MFA, RBAC, SSO.
- Not publicly stated.
Integrations & Ecosystem
IronNet focuses on the “triage” and “intelligence” side of the security house.
- CrowdStrike
- Microsoft Sentinel
- Splunk
- Palo Alto Networks
Support & Community
IronNet offers 24/7 support and is a leader in global threat research and public-private partnerships.
9 — Plixer Scrutinizer
Short description: Scrutinizer is a high-performance NDR tool that leverages NetFlow and metadata to provide immense scalability and forensic depth.
Key Features
- Metadata Collection: Collects and stores flow data from every corner of the network.
- Rapid Reporting: Can generate reports on billions of flows in seconds.
- Malware Detection: Uses behavioral models to identify C2 and data exfiltration.
- Policy Enforcement: Monitors if network flows are violating internal security policies.
- Cloud Support: Ingests flow logs from AWS, Azure, and Google Cloud.
- Historical Analysis: Provides one of the longest retention periods for flow metadata.
Pros
- Unrivaled for forensic historical searches across massive networks.
- Very low performance overhead as it uses existing network telemetry.
Cons
- Less focused on “autonomous response” compared to tools like Darktrace.
- Lacks the deep packet inspection (DPI) of full packet capture tools.
Platforms / Deployment
- Windows / Linux / Web
- Physical appliance / Virtual / Cloud
Security & Compliance
- SSO, RBAC.
- Not publicly stated.
Integrations & Ecosystem
Plixer focuses on being the “forensic engine” for the enterprise.
- Cisco and Juniper
- Splunk
- Check Point
- Gigamon
Support & Community
Plixer provides specialized training, 24/7 technical support, and extensive documentation for network engineers.
10 — Flowmon
Short description: Flowmon (by Progress) provides a unified solution for network performance monitoring and security through behavioral analysis.
Key Features
- Anomaly Detection Engine: Finds zero-day threats and botnets through traffic patterns.
- Network Performance Monitoring: Integrated tools to find bottlenecks and outages.
- DDoS Protection: Specialized modules to detect and mitigate volume-based attacks.
- Encrypted Traffic Analysis: Analyzes TLS metadata to find risky certificates.
- Virtual and Cloud Sensors: Ingests data from physical taps or cloud mirroring.
- Interactive Dashboards: Provides high-level business views and deep-dive technical views.
Pros
- Combines “Security” and “Operations” into a single, cost-effective tool.
- Very easy to deploy and manage for mid-sized enterprise teams.
Cons
- Response capabilities are more manual compared to AI-driven competitors.
- May not have the same level of “threat hunting” sophistication as Vectra or Darktrace.
Platforms / Deployment
- Linux / Web
- Physical appliance / Virtual / Cloud
Security & Compliance
- RBAC, Encryption.
- Not publicly stated.
Integrations & Ecosystem
Flowmon is designed to be a versatile player in the network management space.
- Cisco and Check Point
- Microsoft Azure
- Splunk
- IBM QRadar
Support & Community
Flowmon offers 24/7 support, a professional partner network, and an extensive library of video tutorials.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| Darktrace | Autonomous Response | Windows, macOS, Linux | Hybrid | Self-Learning AI | 4.6/5 |
| Vectra AI | Attacker Behavior | Web, Cloud | Hybrid | AI-Assisted Triage | 4.5/5 |
| ExtraHop Reveal(x) | Decrypted Visibility | Web, Cloud | Hybrid | Line-Rate Decryption | 4.7/5 |
| Cisco Secure | Large Cisco Networks | Windows, Linux | Hybrid | Flow-Based Scale | 4.2/5 |
| Corelight | Open-Source Flexibility | Linux, Windows | Hybrid | Zeek-Powered Telemetry | 4.8/5 |
| Arista Awake | IoT & Entity Tracking | Web, Windows | Hybrid | Entity Fingerprinting | 4.6/5 |
| Fidelis Network | DLP & Network Security | Windows, Linux | Hybrid | Deep Session Inspection | 4.3/5 |
| IronNet IronDefense | Collective Defense | Windows, Linux | Hybrid | IronDome Community | N/A |
| Plixer Scrutinizer | Forensic Scalability | Windows, Linux | Hybrid | High-Speed Reporting | 4.4/5 |
| Flowmon | Security + Performance | Linux, Web | Hybrid | Performance Monitoring | 4.5/5 |
Evaluation & Scoring of Network Detection & Response
The scoring model below evaluates the top NDR tools based on critical performance metrics.
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| Darktrace | 10 | 6 | 9 | 9 | 8 | 9 | 7 | 8.40 |
| Vectra AI | 9 | 7 | 9 | 8 | 9 | 9 | 8 | 8.55 |
| ExtraHop | 10 | 6 | 9 | 9 | 10 | 9 | 7 | 8.60 |
| Cisco Secure | 7 | 8 | 10 | 9 | 8 | 10 | 9 | 8.35 |
| Corelight | 9 | 5 | 10 | 9 | 9 | 8 | 8 | 8.20 |
| Arista Awake | 9 | 7 | 8 | 9 | 9 | 8 | 8 | 8.25 |
| Fidelis | 8 | 6 | 8 | 8 | 8 | 8 | 9 | 7.85 |
| IronNet | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.70 |
| Plixer | 7 | 8 | 9 | 8 | 10 | 8 | 9 | 8.25 |
| Flowmon | 8 | 9 | 8 | 8 | 8 | 8 | 10 | 8.35 |
Scoring Interpretation:
The weighted total indicates that while ExtraHop and Vectra AI lead in technical depth and investigative power, Cisco and Flowmon offer superior value and ease for generalized network monitoring. Darktrace remains the top choice for organizations prioritizing autonomous mitigation over manual triage.
Which Network Detection & Response Tool Is Right for You?
Solo / Freelancer
Network Detection and Response is typically an enterprise-grade solution. For a freelancer or very small team, a full NDR suite is likely unnecessary. Instead, consider using the open-source version of Zeek or a high-quality firewall with basic intrusion detection features.
SMB
For mid-sized businesses with limited security staff, Flowmon or Vectra AI are the best choices. They provide high-value alerts without requiring a massive infrastructure or a dedicated team of network forensic experts.
Mid-Market
Organizations that are scaling their security operations should look at Cisco Secure Network Analytics (if already using Cisco hardware) or ExtraHop Reveal(x). These tools provide the throughput needed for growing data centers and offer strong automated response options.
Enterprise
Global enterprises with complex hybrid-cloud environments and high risk profiles should prioritize Darktrace, Arista Awake Security, or ExtraHop. These platforms provide the most advanced AI-driven detection and entity tracking to combat state-sponsored attackers.
Budget vs Premium
- Budget: Flowmon or Plixer Scrutinizer (especially if leveraging existing flow logs).
- Premium: Darktrace or ExtraHop Reveal(x) with full decryption modules.
Feature Depth vs Ease of Use
- Deep Depth: Corelight (via Zeek scripting) and ExtraHop.
- Easy to Use: Darktrace and Cisco Secure (due to automation).
Integrations & Scalability
- Top Integrations: Cisco and Corelight.
- Top Scalability: Cisco and Plixer Scrutinizer.
Security & Compliance Needs
Organizations requiring strict compliance (HIPAA, FedRAMP) should evaluate ExtraHop or Darktrace, as they provide the best combination of data encryption and detailed audit logging.
Frequently Asked Questions (FAQs)
1. What is the main difference between NDR and EDR?
EDR (Endpoint Detection and Response) monitors activities on individual devices like laptops and servers. NDR monitors the communication between those devices across the network. NDR is essential because it can detect threats on devices that can’t run an EDR agent, such as printers, IoT devices, and unmanaged BYOD hardware.
2. Can NDR tools see into encrypted traffic?
Most modern NDR tools use one of two methods: Encrypted Traffic Analysis (ETA), which looks at metadata like packet headers and timing to find threats without decryption, or full SSL/TLS decryption, where the tool acts as a middleman to inspect the actual contents of the packets.
3. How does NDR help with Zero Trust?
In a Zero Trust architecture, no communication is trusted by default. NDR acts as the continuous monitoring layer that ensures only authorized flows are occurring and that any device attempting to communicate outside its permitted segment is instantly identified and blocked.
4. Is NDR the same as an Intrusion Detection System (IDS)?
NDR is the evolution of IDS. While an IDS looks for known bad signatures (like a virus scanner), NDR uses behavioral analytics and AI to find unknown “zero-day” threats and focuses heavily on the “Response” part of the security cycle.
5. Does NDR require a lot of bandwidth?
Traditional packet-capture NDR can be bandwidth-intensive, but many tools now use “metadata” or “flow logs” (NetFlow/IPFIX), which provide high visibility with less than 1% impact on network performance, making them suitable for even the largest global networks.
6. Can NDR detect threats in the cloud?
Yes, most top-tier NDR tools offer virtual sensors or cloud-native integrations that ingest flow logs from AWS, Azure, and Google Cloud. This allows for a unified security view that covers both the physical office and the virtual cloud infrastructure.
7. How long should network metadata be stored?
For forensic purposes, most security experts recommend storing network metadata for at least 30 to 90 days. This allows analysts to go back in time and see if an attacker was present in the network weeks before a breach was discovered.
8. Does NDR replace the need for a SIEM?
No, NDR and SIEM (Security Information and Event Management) are complementary. The SIEM collects logs from everything (firewalls, endpoints, cloud), while the NDR provides the deep, high-fidelity network data that the SIEM often misses.
9. What is lateral movement and why is it important for NDR?
Lateral movement is when an attacker moves from a compromised computer to other parts of the network to find sensitive data. NDR is the best tool for detecting this because lateral movement always leaves a footprint on the internal network that perimeter firewalls cannot see.
10. How difficult is it to deploy an NDR solution?
Deployment varies; flow-based tools (like Cisco) can be enabled on existing hardware in hours. Packet-capture tools (like Darktrace or ExtraHop) require physical or virtual appliances to be installed at strategic “choke points” in the network, which can take several days to tune.
Conclusion
Network Detection and Response is the “eye in the sky” for the modern security operations center. While endpoints and identities are vital, the network is the one place where attackers cannot hide their actions. Whether you prioritize the autonomous response of Darktrace, the wire-data depth of ExtraHop, or the open-source power of Corelight, an NDR solution is essential for moving from a reactive to a proactive security posture. As you evaluate your options, focus on the tools that integrate best with your existing stack and offer the scalability to grow with your digital transformation