Find the Best Cosmetic Hospitals — Choose with Confidence
Discover top cosmetic hospitals in one place and take the next step toward the look you’ve been dreaming of.
“Your confidence is your power — invest in yourself, and let your best self shine.”
Compare • Shortlist • Decide smarter — works great on mobile too.
Introduction
Bot management tools are specialized cybersecurity solutions designed to identify, categorize, and mitigate automated web traffic. In the current digital landscape, bots account for nearly half of all internet traffic, ranging from “good” bots (like search engine crawlers) to “bad” bots (such as those used for credential stuffing, price scraping, and inventory hoarding). These platforms utilize a combination of behavioral analysis, machine learning, and fingerprinting to distinguish between human users and automated scripts in real-time, allowing legitimate traffic to pass through while blocking or challenging malicious actors.
As we navigate through, the sophistication of automated threats has reached an all-time high. The democratization of generative AI has enabled attackers to create “human-mimicking” bots that can bypass traditional CAPTCHAs and basic rate-limiting rules. Modern bot management is no longer just about blocking IP addresses; it is about protecting the integrity of business logic, preventing account takeovers (ATO), and ensuring that server resources are not drained by non-human traffic. Organizations now prioritize “invisible” challenges that maintain a frictionless user experience while simultaneously increasing the cost for attackers to operate.
Real-world use cases:
- E-commerce Protection: Preventing “scalper bots” from hoarding limited-edition inventory or scraping proprietary pricing data.
- Account Security: Defending login portals against large-scale credential stuffing and brute-force attacks.
- API Security: Safeguarding the mobile and web APIs that power modern applications from automated abuse.
- Marketing Integrity: Ensuring that advertising budgets are not wasted on fraudulent bot clicks and that lead-generation forms are not filled with spam.
- Content Protection: Stopping unauthorized scraping of copyrighted content, news articles, or intellectual property.
Evaluation criteria for buyers:
- Detection Efficacy: The ability to identify sophisticated “Gen 4” and “Gen 5” bots that mimic human behavior.
- False Positive Rate: The frequency at which legitimate human users are incorrectly blocked or challenged.
- Deployment Flexibility: Support for edge, cloud-native, on-premises, or hybrid architectures.
- Real-time Mitigation: The latency introduced by the inspection process and the speed of the blocking action.
- User Experience Impact: The use of low-friction challenges (like private access tokens) instead of intrusive CAPTCHAs.
- Threat Intelligence: The depth and freshness of the vendor’s global database of known bot signatures and IP reputations.
- Granular Reporting: The quality of the dashboards and the ability to “drill down” into specific attack vectors.
- API and Mobile Support: Specialized protection for non-browser environments which are often high-value targets.
- Integration Ecosystem: How well the tool connects with existing WAFs, SIEMs, and load balancers.
- Total Cost of Ownership: The balance between subscription fees and the reduction in infrastructure costs and fraud losses.
Mandatory Paragraph
- Best for: Enterprise organizations, high-traffic e-commerce platforms, financial institutions, and SaaS providers who handle sensitive user data and high-value transactions.
- Not ideal for: Small personal blogs with minimal traffic, static internal sites with no public-facing forms, or businesses looking for simple, one-time firewall rules without ongoing management.
Key Trends in Bot Management
- Behavioral Biometrics 2.0: Moving beyond mouse movements to analyze hundreds of subtle physiological signals to verify human presence.
- GenAI-Powered Bot Defense: Utilizing Large Language Models (LLMs) to predict attack patterns and update detection logic before an attack even begins.
- Frictionless Verification: A total shift away from traditional visual CAPTCHAs toward background proof-of-work challenges and hardware-backed attestations.
- API-First Security Architecture: Recognizing that bots have moved from browser-based attacks to direct API exploitation, requiring deep packet inspection at the interface level.
- Edge-Native Mitigation: Executing bot detection logic at the network edge (e.g., via WebAssembly) to eliminate latency and stop bots before they reach the origin server.
- Automated Fraud Intelligence Sharing: Real-time synchronization of threat data between different vendors and platforms to create a “global immune system” against bots.
- Supply Chain Bot Defense: Protecting the third-party scripts and libraries integrated into websites from being leveraged by automated attackers.
- Regulatory Compliance Focus: Ensuring bot mitigation strategies comply with evolving global privacy laws (GDPR, CCPA) by minimizing personal data collection.
How We Selected These Tools (Methodology)
The selection of the top 10 bot management platforms was driven by a comprehensive evaluation of technical performance and market reliability. The methodology included:
- Detection Sophistication: We prioritized tools that demonstrate the ability to handle polymorphic bots and headless browsers.
- Market Share & Mindshare: We analyzed the tools most frequently deployed by the Fortune 500 and high-growth technology leaders.
- Performance Overhead: We evaluated the latency impact each tool has on the end-user experience during the inspection phase.
- Enterprise Features: The inclusion of RBAC, SSO, and multi-tenant management was a critical requirement for high-ranking tools.
- Independent Validation: We reviewed performance data from third-party security labs and industry analysts.
- Adaptability: We focused on tools that offer a variety of response actions (Block, Challenge, Rate-limit, Deceive).
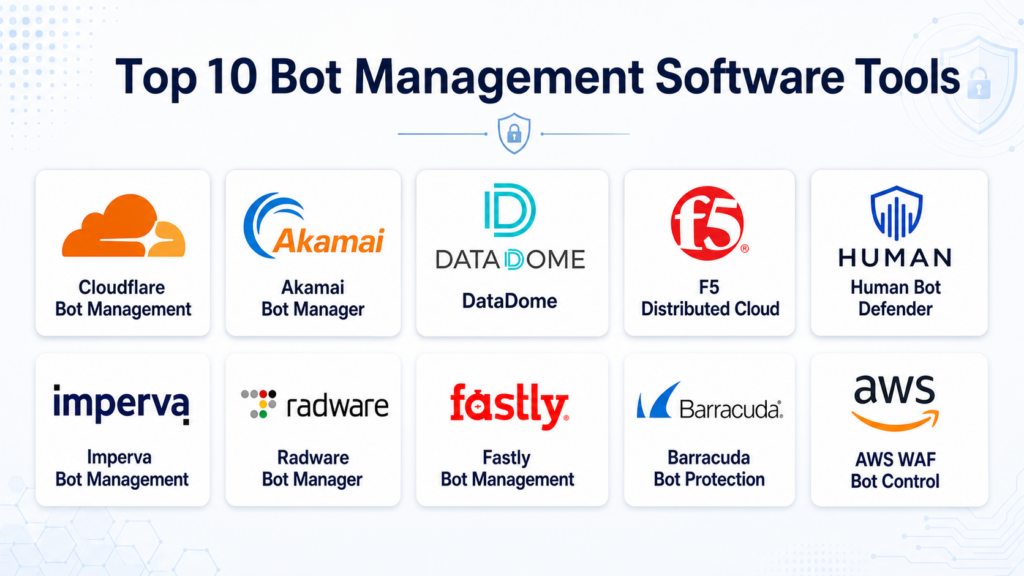
Top 10 Bot Management Software Tools
#1 — Cloudflare Bot Management
Short description: A highly scalable solution integrated directly into Cloudflare’s global network, providing massive threat intelligence and sub-millisecond detection.
Key Features
- Global Threat Intelligence: Leverages data from millions of websites to identify bot patterns instantly.
- Behavioral Analysis: Uses machine learning to build a “bot score” for every request based on subtle behavior cues.
- Turnstile: A modern, privacy-preserving CAPTCHA replacement that verifies humans without visual puzzles.
- Verified Bot Directory: Automatically allows “good” bots (like Google) while filtering malicious ones.
- Fingerprinting: Advanced client-side signals that identify automated environments even when they rotate IPs.
- API Shield: Specialized protection for API endpoints, preventing automated scraping and data exfiltration.
Pros
- Extremely easy to deploy for existing Cloudflare users with a simple “toggle” approach.
- Native integration with WAF and CDN reduces overall latency.
Cons
- Can be expensive for very high-traffic volumes if not on an Enterprise plan.
- Advanced customization options are restricted to higher-tier customers.
Platforms / Deployment
- Cloud / Edge
- SaaS
Security & Compliance
- SSO/SAML, MFA, RBAC.
- SOC 2 Type II, ISO 27001, PCI DSS, GDPR.
Integrations & Ecosystem
Cloudflare offers a vast ecosystem of native integrations and APIs.
- Terraform / Pulumi
- Splunk / Datadog / Logflare
- Major Cloud Providers (AWS, Azure, GCP)
Support & Community
Extensive documentation, community forums, and 24/7/365 enterprise support with strict SLAs.
#2 — Akamai Bot Manager
Short description: A premier enterprise-grade solution that utilizes one of the world’s largest distributed platforms to provide deep visibility and mitigation.
Key Features
- Akamai Intelligent Edge: Processes traffic at the massive scale of the Akamai CDN.
- Sophisticated Fingerprinting: Collects hundreds of signals to identify the most advanced bots.
- Human-Interaction Analysis: Monitors keyboard behavior and device orientation to verify human users.
- Bot Directory: A curated list of over 1,500 “known bots” with granular controls.
- Advanced Reporting: High-fidelity analytics that help distinguish between different bot generations.
- Mobile SDK: Specialized protection for mobile applications to prevent automated app abuse.
Pros
- Unrivaled efficacy for large-scale enterprise environments.
- Excellent at protecting high-value business logic from complex scraping.
Cons
- Implementation can be complex and typically requires professional service hours.
- The pricing structure is generally higher than cloud-native alternatives.
Platforms / Deployment
- Cloud / Edge
- Hybrid
Security & Compliance
- MFA, SSO, RBAC.
- SOC 2, ISO 27001, HIPAA, FedRAMP.
Integrations & Ecosystem
Designed to work with the broader Akamai security and delivery suite.
- SIEM connectors for QRadar and ArcSight.
- Web and Mobile SDKs.
- Advanced API protection modules.
Support & Community
World-class global support team (SOCC) providing proactive monitoring and incident response.
#3 — DataDome
Short description: A specialist bot management solution that focuses on real-time detection at the edge with zero impact on the user experience.
Key Features
- Real-time AI Detection: Analyzes every single request in under 2 milliseconds.
- Autopilot: A fully automated mode that handles bot mitigation without manual intervention.
- Specialized CAPTCHA: An integrated, privacy-focused CAPTCHA that only triggers for high-risk requests.
- Multi-Cloud Protection: Deployable across any cloud provider, CDN, or server architecture.
- Comprehensive Dashboards: Provides detailed insights into the intent of the bots (Scraping, ATO, etc.).
- API Security: Deep inspection of API traffic to stop automated abuse of backend services.
Pros
- High detection rates with very low false positives.
- Exceptional “time-to-value” with a fast and straightforward setup.
Cons
- Being a specialist tool, it requires integration with your existing CDN/WAF if you want a single pane of glass.
- Reporting can sometimes feel less customizable compared to broader security suites.
Platforms / Deployment
- Cloud / Edge / On-premises / Hybrid
- SaaS
Security & Compliance
- SSO, RBAC.
- SOC 2, GDPR, CCPA.
Integrations & Ecosystem
DataDome offers a wide array of “connectors” for modern stacks.
- AWS Lambda@Edge / CloudFront
- Nginx / Apache / IIS
- Salesforce Commerce Cloud
- Fastly / Varnish
Support & Community
Responsive technical support and a strong reputation for customer success.
#4 — F5 Distributed Cloud Bot Defense
Short description: Formerly known as Shape Security, this platform is widely considered the “gold standard” for protecting large-scale financial and retail login pages.
Key Features
- AI/ML Analysis: Uses massive datasets to identify even the most subtle bot signatures.
- Predictive Defense: Stops automated attacks before they reach the application.
- Behavioral Biometrics: Analyzes how users interact with pages to find non-human patterns.
- Mobile App Protection: Deep SDK-based integration for mobile-first organizations.
- Managed Services: F5 experts actively monitor and tune the defense for the customer.
- Retroactive Analysis: Ability to analyze past logs to find hidden bot activity.
Pros
- Arguably the highest detection efficacy for credential stuffing in the industry.
- Significantly reduces the cost of fraud for large enterprises.
Cons
- High premium cost makes it inaccessible for smaller organizations.
- Requires significant engineering effort for initial integration and SDK deployment.
Platforms / Deployment
- Cloud / Edge / On-premises / Hybrid
- SaaS / Managed Service
Security & Compliance
- Enterprise-grade security controls.
- SOC 2, ISO 27001, PCI DSS.
Integrations & Ecosystem
Integrates with the F5 BIG-IP ecosystem and modern cloud platforms.
- F5 BIG-IP
- NGINX
- Major Cloud Service Providers
Support & Community
Top-tier professional services and 24/7 dedicated support centers.
#5 — Human Bot Defender
Short description: Part of the HUMAN (formerly White Ops) Modern Defense Platform, this tool focuses on verifying humanity across the entire digital journey.
Key Features
- Verification Engine: Uses a “Human Stack” to verify users at over 2,500 signals.
- Threat Intelligence: Monitors trillions of interactions monthly across the internet.
- Adaptive Challenges: Deploys challenges that adapt based on the risk profile of the request.
- Inventory Protection: Specialized modules to prevent hoarding and scraping in retail.
- Satori Threat Intelligence: Dedicated research team that proactively finds new botnets.
- Account Takeover Protection: Deep focus on securing the identity perimeter.
Pros
- Extremely accurate detection with a focus on “humanity” rather than just “bot-ness.”
- Excellent transparency in reporting and forensic data.
Cons
- Integration can be technical, particularly for mobile applications.
- Primarily focused on large enterprise customers.
Platforms / Deployment
- Cloud / Edge
- SaaS
Security & Compliance
- SSO, MFA.
- SOC 2, ISO 27001.
Integrations & Ecosystem
Works across a variety of marketing and security stacks.
- AWS / Azure / GCP
- Fastly / Cloudflare
- Google Marketing Platform
Support & Community
Highly specialized support team with deep expertise in cybercrime and fraud.
#6 — Imperva Bot Management
Short description: Integrated into the Imperva Web Application & API Protection (WAAP) stack, it provides a unified approach to application security.
Key Features
- Unified WAAP: Combines WAF, DDoS, API Security, and Bot Management in one platform.
- Behavioral Analysis: Uses ML to distinguish between humans, “good” bots, and “bad” bots.
- CAPTCHA-free Challenges: Minimizes user friction through background browser verification.
- Community Defense: Leverages threat data from across the entire Imperva customer base.
- Advanced Bot Classification: Categorizes bots by their specific intent (e.g., ad fraud, scraping).
- Integration with SIEM: Easy exporting of data for deeper security analysis.
Pros
- Excellent value for organizations looking for a “one-stop shop” for application security.
- Strong reporting that highlights the business impact of bot traffic.
Cons
- Bot detection might not be as “bleeding edge” as specialized startups like DataDome.
- The interface can be complex due to the breadth of features in the WAAP stack.
Platforms / Deployment
- Cloud / Edge / On-premises
- SaaS
Security & Compliance
- RBAC, MFA, SSO.
- SOC 2, ISO 27001, PCI DSS.
Integrations & Ecosystem
Strongest when used within the Imperva ecosystem.
- Splunk / Arcsight
- Terraform
- AWS / Azure / GCP
Support & Community
Robust global support network and a mature customer success program.
#7 — Radware Bot Manager
Short description: A versatile platform known for its flexible deployment options and strong protection against account takeover and API abuse.
Key Features
- Intent-based Detection: Focuses on the “why” behind the bot’s activity.
- Collective Intelligence: Shares threat data across all Radware deployments in real-time.
- Non-Intrusive Mitigation: Uses transparent challenges to verify users without interruption.
- Flexible Deployment: Can be deployed as a cloud service, on-prem appliance, or virtual machine.
- API Protection: Specialized detection for headless browser activity targeting APIs.
- Deep Forensic Data: Provides logs for every single request for post-incident analysis.
Pros
- Exceptional deployment flexibility for organizations with unique infrastructure.
- Strong focus on technical accuracy and minimizing false positives.
Cons
- The management console can feel a bit dated compared to modern SaaS rivals.
- Requires a more technical team to manage and tune compared to “autopilot” solutions.
Platforms / Deployment
- Cloud / Edge / On-premises / Hybrid
- SaaS / Appliance
Security & Compliance
- Standard enterprise security controls.
- SOC 2, ISO 27001.
Integrations & Ecosystem
Integrates well with both legacy and cloud-native infrastructure.
- F5 / Citrix
- AWS / Azure / GCP
- NGINX
Support & Community
Reliable technical support and a long history of serving the enterprise market.
#8 — Fastly Bot Management
Short description: A modern, edge-centric bot solution that leverages the high-performance Fastly platform and Signal Sciences technology.
Key Features
- Edge Mitigation: Executes detection and blocking at the Fastly network edge.
- Signal Sciences Technology: Uses a patented “SmartAgent” for high-fidelity detection.
- Developer-First Design: Provides extensive APIs and CLI tools for automation.
- Low Latency: Optimized for performance-sensitive applications.
- Granular Rules: Allows developers to write custom VCL or WebAssembly logic for bot handling.
- Real-time Analytics: Instant visibility into bot trends as they happen.
Pros
- Incredibly fast performance with minimal overhead.
- Favored by developers for its transparency and control.
Cons
- The “build-it-yourself” flexibility might be overwhelming for non-technical teams.
- Requires a Fastly CDN or WAF deployment to be most effective.
Platforms / Deployment
- Cloud / Edge
- SaaS
Security & Compliance
- SSO, MFA, RBAC.
- SOC 2, ISO 27001, PCI DSS.
Integrations & Ecosystem
Highly integrated with modern DevOps pipelines.
- Terraform
- Slack / PagerDuty
- Datadog / Splunk
Support & Community
Excellent technical support and a strong community presence in the open-source and web-performance worlds.
#9 — Barracuda Bot Protection
Short description: An accessible and robust bot management solution that is part of the Barracuda Web Application Firewall ecosystem.
Key Features
- Cloud-based AI: Uses machine learning to detect and block malicious automated traffic.
- Bot Spam Protection: Specifically targets automated form submissions and comment spam.
- Credential Stuffing Defense: Protects login pages from brute-force automated attacks.
- Ease of Management: Designed for IT teams that need effective protection without high complexity.
- Integrated WAF: Part of a broader application security suite.
- Threat Intelligence: Leverages Barracuda’s global sensor network.
Pros
- Strong price-to-performance ratio for mid-market organizations.
- Straightforward interface that is easy to navigate.
Cons
- May lack the depth of behavioral analysis found in “Tier 1” enterprise tools.
- Reporting is functional but less “forensic” than specialized competitors.
Platforms / Deployment
- Cloud / On-premises
- SaaS / Virtual Appliance
Security & Compliance
- Standard security protocols.
- SOC 2.
Integrations & Ecosystem
Works best within the Barracuda and Microsoft Azure environments.
- Microsoft Azure (native integration)
- AWS / GCP
- Barracuda Cloud Control
Support & Community
Good reputation for customer service and technical support.
#10 — AWS WAF Bot Control
Short description: A cloud-native bot management feature built directly into the AWS WAF service, offering seamless integration for AWS-centric workloads.
Key Features
- Managed Rule Groups: AWS-maintained rules that identify common bots and scrapers.
- Targeted Bot Protection: Specialized rules for protecting login pages and APIs.
- Dashboard Integration: Visibility through AWS CloudWatch and WAF dashboards.
- Pay-as-you-go: Consumption-based pricing with no upfront commitments.
- Native Integration: Works directly with CloudFront, ALB, and API Gateway.
- Custom Rules: Ability to combine bot rules with your own custom WAF logic.
Pros
- Zero integration effort for companies already using AWS WAF.
- Extremely cost-effective for smaller workloads or specific endpoint protection.
Cons
- Lacks the advanced behavioral biometrics and “humanity verification” of dedicated platforms.
- Detection capabilities are generally considered more “reactive” than “proactive.”
Platforms / Deployment
- Cloud (AWS only)
- SaaS
Security & Compliance
- IAM, MFA, CloudTrail.
- SOC 1/2/3, ISO 27001, FedRAMP, HIPAA.
Integrations & Ecosystem
Strictly within the AWS ecosystem.
- Amazon CloudFront
- Application Load Balancer (ALB)
- Amazon API Gateway
- AWS AppSync
Support & Community
Standard AWS support plans and a massive global community of AWS practitioners.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| Cloudflare Bot Management | Performance/Global Scale | Cloud, Edge | SaaS | Turnstile (Frictionless) | 4.8/5 |
| Akamai Bot Manager | Large Enterprises | Cloud, Edge, Hybrid | Hybrid | Global Threat Intelligence | 4.7/5 |
| DataDome | Real-time Detection | Cloud, Edge, On-prem | SaaS | 2ms Latency Guarantee | 4.9/5 |
| F5 Distributed Cloud | Financial/Retail Login | Cloud, Edge, On-prem | Managed | Behavioral Biometrics | 4.8/5 |
| Human Bot Defender | Humanity Verification | Cloud, Edge | SaaS | Human Stack Intelligence | 4.7/5 |
| Imperva Bot Management | Unified WAAP Security | Cloud, Edge, On-prem | SaaS | intent-based Analytics | 4.5/5 |
| Radware Bot Manager | Flexible Deployment | Cloud, Edge, On-prem | Appliance | Intent-based Detection | 4.4/5 |
| Fastly Bot Management | Developer/Edge Perf | Cloud, Edge | SaaS | SmartAgent Technology | 4.6/5 |
| Barracuda Bot Protection | Mid-Market/Azure Users | Cloud, On-prem | SaaS | Simple Configuration | 4.2/5 |
| AWS WAF Bot Control | AWS Native Workloads | Cloud (AWS) | SaaS | Pay-as-you-go Pricing | 4.1/5 |
Evaluation & Scoring of Bot Management Tools
The scoring below is based on the comparative strengths of each platform in a high-stakes 2026 environment.
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| Cloudflare Bot Mgmt | 9 | 10 | 10 | 9 | 10 | 9 | 9 | 9.40 |
| Akamai Bot Manager | 10 | 6 | 9 | 10 | 9 | 10 | 7 | 8.65 |
| DataDome | 10 | 9 | 9 | 9 | 10 | 9 | 9 | 9.30 |
| F5 Distributed Cloud | 10 | 5 | 8 | 10 | 9 | 10 | 7 | 8.35 |
| Human Bot Defender | 9 | 7 | 8 | 10 | 9 | 9 | 8 | 8.55 |
| Imperva Bot Mgmt | 8 | 8 | 9 | 9 | 8 | 9 | 9 | 8.45 |
| Radware Bot Manager | 8 | 7 | 8 | 9 | 8 | 8 | 8 | 7.85 |
| Fastly Bot Management | 9 | 8 | 9 | 9 | 10 | 9 | 8 | 8.85 |
| Barracuda Bot Prot | 7 | 9 | 7 | 8 | 8 | 8 | 9 | 7.85 |
| AWS WAF Bot Control | 6 | 10 | 7 | 8 | 9 | 8 | 10 | 7.85 |
Scoring Interpretation:
- Core (25%): Efficacy of bot detection and mitigation logic.
- Ease (15%): Speed of deployment and management effort.
- Integrations (15%): Support for modern tech stacks and third-party tools.
- Weighted Total: A calculated score where $Total = \sum (Score_i \times Weight_i)$, representing the overall platform utility.
Which Bot Management Tool Is Right for You?
Solo / Freelancer
If you are managing a small personal project or a high-traffic blog, AWS WAF Bot Control or Cloudflare’s Free/Pro Bot Fight Mode are your best options. They provide basic protection with zero to low cost and require no technical configuration.
SMB
For small to medium businesses that need reliable protection against scraping and spam, Barracuda Bot Protection or DataDome offer the best balance of ease-of-use and technical efficacy. These tools are “set it and forget it” while providing professional-grade reporting.
Mid-Market
Companies that are scaling quickly and have diverse infrastructure should look at Cloudflare Bot Management or Fastly Bot Management. These platforms grow with you and offer the developer-level control needed for customized workflows.
Enterprise
For organizations with high-value targets (Banking, Luxury Retail, Airlines), Akamai Bot Manager, F5 Distributed Cloud Bot Defense, or Human Bot Defender are essential. These tools provide the deep behavioral analysis and managed services required to stop elite, custom-built botnets.
Budget vs Premium
- Budget: AWS WAF Bot Control, Cloudflare (Pro Tier).
- Premium: F5 Distributed Cloud, Akamai Bot Manager, Human.
Feature Depth vs Ease of Use
- Highest Depth: Akamai Bot Manager, F5.
- Easiest to Use: DataDome, Cloudflare, AWS WAF.
Integrations & Scalability
- Best Integrations: Cloudflare, DataDome.
- Best Scalability: Akamai, Fastly.
Security & Compliance Needs
Organizations with high regulatory requirements (Government, Healthcare) should prioritize Akamai or Cloudflare, as they maintain the most extensive list of global compliance certifications.
Frequently Asked Questions (FAQs)
1. What is the difference between a WAF and a Bot Management tool?
A Web Application Firewall (WAF) primarily looks for known vulnerabilities in code (like SQL injection or XSS) using signature-based rules. Bot Management tools focus on the “identity” and “behavior” of the requester to determine if they are a human or an automated script, even if the request itself looks technically perfect.
2. Can bot management tools distinguish between “good” and “bad” bots?
Yes, modern tools maintain a verified bot directory. This ensures that essential automated traffic—such as Google search crawlers, social media preview bots, and performance monitors—can access the site while malicious scrapers and credential stuffers are blocked.
3. Do these tools slow down my website for human users?
Most modern solutions (like DataDome or Cloudflare) execute their logic at the edge or asynchronously, meaning the latency added is typically under 5 milliseconds. This is virtually imperceptible to a human user and is often offset by the performance gain of removing heavy bot traffic from your origin servers.
4. Are CAPTCHAs still necessary for bot defense?
While traditional visual CAPTCHAs are being phased out due to poor user experience and AI-driven solving, “invisible” challenges are the new standard. These run in the background of the browser to verify humanity without requiring the user to solve puzzles.
5. How do bots bypass traditional security measures?
Advanced bots use “headless browsers” (like Puppeteer or Playwright) that execute JavaScript and mimic human-like mouse movements. They also use residential proxy networks to rotate thousands of real IP addresses, making simple rate-limiting and IP-blocking ineffective.
6. What is “Credential Stuffing” and how do these tools stop it?
Credential stuffing is when bots try millions of stolen username/password pairs across different sites. Bot management tools stop this by identifying the high-velocity, automated nature of the login attempts and applying challenges or blocks before the bot can validate a single account.
7. Is it possible for a bot management tool to block real human users?
Yes, this is known as a “false positive.” High-quality tools minimize this by using behavioral scoring. Instead of a hard block, they often issue a “challenge” (like a silent proof-of-work) that a human user’s browser will pass automatically, ensuring they never see a block page.
8. Can I use these tools to protect mobile applications?
Yes, but it usually requires the integration of a Mobile SDK provided by the vendor (e.g., Akamai, F5, or DataDome). This allows the tool to verify the integrity of the mobile device and the application environment itself.
9. How does pricing typically work for bot management?
Pricing varies by vendor but is usually based on either the number of requests inspected, the number of protected monthly active users (MAU), or a flat subscription fee based on the feature set and support level.
10. Do I need a dedicated team to manage these tools?
While enterprise-level tools (Akamai, F5) may require regular tuning by a security professional, many modern SaaS solutions (DataDome, Cloudflare) are designed with “autopilot” modes that can handle the vast majority of threats without manual intervention.
Conclusion
Bot management has evolved from a “nice-to-have” add-on to a mission-critical component of the modern security stack. As attackers leverage AI to create more sophisticated automated threats, the choice of a bot defense partner becomes vital for protecting business revenue and user trust. Whether you choose the massive scale of Cloudflare, the specialized speed of DataDome, or the enterprise depth of Akamai, the goal remains the same: ensuring that your digital experiences are reserved for real humans.