Find the Best Cosmetic Hospitals — Choose with Confidence
Discover top cosmetic hospitals in one place and take the next step toward the look you’ve been dreaming of.
“Your confidence is your power — invest in yourself, and let your best self shine.”
Compare • Shortlist • Decide smarter — works great on mobile too.
Introduction
Third‑Party Risk Management (TPRM) Tools are specialized software platforms that help organizations identify, assess, monitor, and mitigate risks introduced by external third parties — including suppliers, vendors, contractors, service providers, and partners. These tools centralize risk data, automate assessments, track controls and compliance, provide real‑time monitoring, and deliver analytics that drive more informed risk decisions. As enterprises rely heavily on external entities for strategic capabilities — such as software services, logistics, data hosting, and staffing — gaps in third‑party oversight can lead to compliance violations, security incidents, financial loss, reputational damage, and operational disruption.
In , regulatory expectations, data privacy laws, extended supply chains, and cyber risk concerns have made systematic third‑party risk governance a board‑level priority. Manual, spreadsheet‑based approaches fail to scale, lack visibility, and are error‑prone. Modern TPRM tools automate risk assessments, streamline vendor lifecycle workflows, centralize evidence and documentation, integrate with enterprise risk and security systems, and provide dashboards that tie risk into procurement and operational processes — helping organizations shift from reactive to proactive risk posture.
Real‑world use cases include:
- Assessing vendor risk using standardized questionnaires and risk scoring models.
- Continuous monitoring of third‑party security posture, compliance, and financial health.
- Automating workflows for onboarding, reassessment, and contract renewals with risk checkpoints.
- Visualizing risk heatmaps, dashboards, and reporting for executives and auditors.
- Integrating with cybersecurity, procurement, and contract systems to unify risk signals.
Evaluation Criteria for Buyers:
- Third‑party onboarding & risk assessment workflows
- Automated questionnaires & risk scoring
- Continuous monitoring & alerting
- Integration with procurement, security, and contract systems
- Analytics, dashboards, and reporting
- Document & evidence management
- Regulatory compliance support (GDPR, SOC 2, ISO, etc.)
- Role‑based access & audit trails
- Scalability and multi‑entity support
- Support, onboarding, and professional services
Best for: Risk management teams, procurement leaders, security and compliance officers, legal departments, supply chain teams, and enterprise governance professionals in regulated industries or organizations with extensive vendor ecosystems.
Not ideal for: Small teams with few third‑party relationships where risk exposures are limited and can be managed manually.
Key Trends in Third‑Party Risk Management (TPRM) Tools
- AI‑driven risk scoring and predictive analytics for early risk identification.
- Continuous risk monitoring via threat feeds, security signals, and compliance data.
- Integration with procurement, finance, and contract lifecycle systems for unified risk control.
- Centralized assessment libraries and dynamic questionnaires for repeatable risk workflows.
- Automated control testing and evidence collection workflows.
- Real‑time dashboards and risk heatmaps for executive and audit visibility.
- Cybersecurity posture integration with vulnerability and threat intelligence.
- Third‑party performance vs. risk benchmarking across industries.
- Regulatory compliance frameworks baked into assessment models.
- Collaborative workflows for review, escalation, and remediation tracking.
How We Selected These Tools (Methodology)
- Evaluated risk lifecycle support from onboarding to remediation and offboarding.
- Assessed assessment engines & risk scoring models for accuracy and flexibility.
- Reviewed continuous monitoring capabilities for security, compliance, finance, and reputation.
- Verified integration breadth with procurement, contract management, security systems, and ERP.
- Checked dashboards, analytics, and reporting maturity.
- Considered workflow automation for approvals, reassessments, and evidence collection.
- Analyzed document & evidence management functionality.
- Assessed security & governance features including RBAC, audit trails, encryption.
- Evaluated scalability from mid‑market to enterprise risk footprints.
- Reviewed support, training, and community resources.
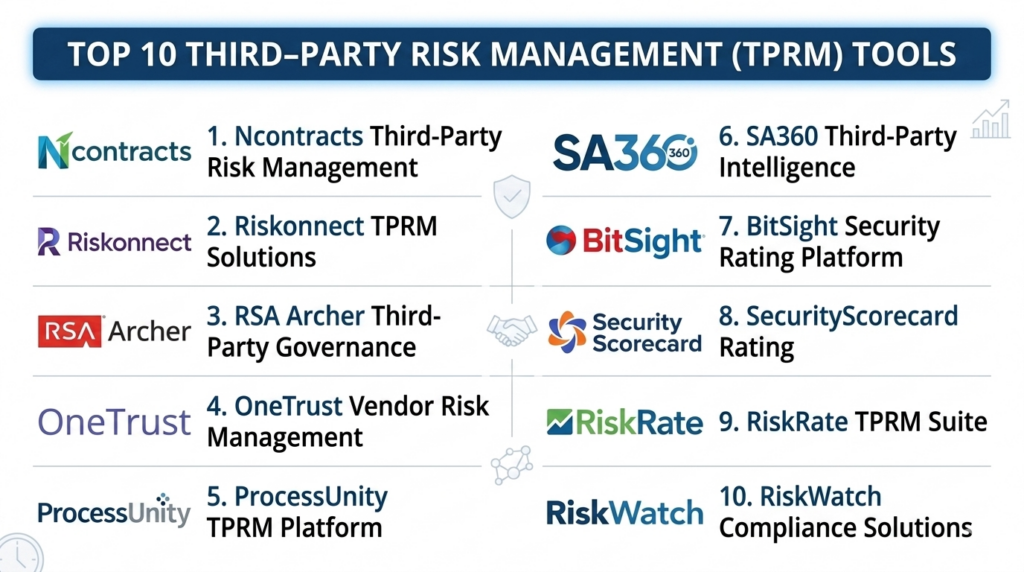
Top 10 Third‑Party Risk Management (TPRM) Tools
#1 — Ncontracts TPRM
Short description:
Ncontracts TPRM delivers an integrated platform for third‑party onboarding, risk assessment, monitoring, and reporting, coupled with compliance frameworks and analytics — widely used in financial services, insurance, and regulated industries.
Key Features
- Vendor risk assessment questionnaires
- Centralized risk scoring & heatmaps
- Continuous monitoring feeds
- Workflow automation for onboarding/ reassessment
- Regulatory compliance templates
Pros
- Strong compliance workflow support
- Integrated analytics & dashboards
- Configurable assessment models
Cons
- Best suited for regulated industries
- Implementation effort varies by scope
Platforms / Deployment
- Web / Cloud
Security & Compliance
- RBAC, encryption, audit trails
Integrations & Ecosystem
- Procurement systems
- Contract management
- Security feeds
Support & Community
- Support and professional services
#2 — Riskonnect Third Party Risk
Short description:
Riskonnect TPRM provides a unified risk management suite with third‑party risk workflows, continuous monitoring, integrated dashboards, and flexible risk scoring — ideal for enterprise risk programs.
Key Features
- Third‑party risk assessments
- Continuous risk monitoring
- Custom risk scoring models
- Central repository & evidence tracking
- Executive dashboards & reporting
Pros
- Unified enterprise risk vision
- Strong analytics and dashboards
- Good configurability
Cons
- Can require configuration effort
- Pricing geared toward larger teams
Platforms / Deployment
- Web / Cloud
Security & Compliance
- Enterprise access controls, encryption
Integrations & Ecosystem
- ERM/IRM systems
- Procurement and security tools
Support & Community
- Support teams
#3 — Archer (RSA Archer Third Party Risk)
Short description:
RSA Archer TPRM is part of the Archer integrated risk management suite, delivering extensive risk workflows, assessments, monitoring, issue management, and reporting — often used in highly regulated enterprises.
Key Features
- Third‑party risk assessments & scorecards
- Compliance and control frameworks
- Continuous monitoring & alerts
- Remediation tracking
- Enterprise risk dashboards
Pros
- Enterprise‑grade risk framework
- Highly configurable
- Deep compliance workflows
Cons
- Implementation and setup can require time
- Advanced features geared to enterprise
Platforms / Deployment
- Web / Cloud
Security & Compliance
- RBAC, encryption, audit logs
Integrations & Ecosystem
- Security, procurement, audit systems
Support & Community
- RSA support resources
#4 — OneTrust Vendor Risk Management
Short description:
OneTrust Vendor Risk Management combines privacy, security, and third‑party risk governance with assessment automation, continuous monitoring, control libraries, remediation workflows, and analytics — popular for privacy‑centric risk programs.
Key Features
- Automated risk assessments
- Control evaluation & evidence collection
- Continuous monitoring
- Remediation workflows
- Dashboards and reporting
Pros
- Strong privacy and security risk coverage
- Extensive integration ecosystem
- Good automation
Cons
- Broad platform can feel complex
- Setup requires planning
Platforms / Deployment
- Web / Cloud
Security & Compliance
- Encryption, compliance frameworks, RBAC
Integrations & Ecosystem
- ITSM, security feeds, procurement
Support & Community
- Documentation & support channels
#5 — ProcessUnity TPRM
Short description:
ProcessUnity offers a cloud‑native TPRM platform with risk assessment automation, control mapping, continuous monitoring, issue remediation, and reporting — designed for enterprise risk and compliance programs.
Key Features
- Questionnaire & assessment automation
- Risk scoring & reporting
- Control mapping
- Monitoring & alerts
- Evidence management
Pros
- Strong risk scoring and control frameworks
- Configurable workflows
- Cloud‑native architecture
Cons
- Advanced modules add cost
- Analytics configuration required
Platforms / Deployment
- Web / Cloud
Security & Compliance
- Encryption, audit trails, RBAC
Integrations & Ecosystem
- Procurement, security integrations
Support & Community
- Support teams
#6 — SAI360 Third Party Risk Management
Short description:
SAI360 provides third‑party risk capabilities within its broader risk and compliance management suite, including onboarding, assessments, monitoring, remediation, and reporting — suitable for regulated industries and enterprise governance.
Key Features
- Supplier risk assessments
- Compliance testing & evidence capture
- Continuous monitoring
- Case management
- Dashboards & analytics
Pros
- Integrated compliance and risk suite
- Good workflow automation
- Strong audit support
Cons
- Enterprise cost profile
- Learning curve for feature depth
Platforms / Deployment
- Web / Cloud
Security & Compliance
- Encryption, role access, audit logs
Integrations & Ecosystem
- ERM, procurement, security
Support & Community
- Support services
#7 — BitSight Third‑Party Risk
Short description:
BitSight TPRM focuses on cybersecurity risk exposure by continuously scoring vendors’ security performance using external threat intelligence, vulnerability data, and security signals.
Key Features
- Cybersecurity risk scores for vendors
- Threat intelligence feeds
- Benchmarking against industry cohorts
- Continuous monitoring
- Alerting and reporting
Pros
- Strong external security signal integration
- Useful benchmarking & alerting
- Continuous visibility
Cons
- Focused primarily on cyber risk
- Not a full vendor risk lifecycle solution
Platforms / Deployment
- Web / Cloud
Security & Compliance
- Risk data encryption and access controls
Integrations & Ecosystem
- Security tools, SIEM, procurement
Support & Community
- Support docs
#8 — SecurityScorecard Third‑Party Risk
Short description:
SecurityScorecard provides continuous vendor security risk monitoring and scoring, threat insights, and benchmarking — widely used by enterprise security and risk teams to understand vendor cyber posture.
Key Features
- Continuous security ratings
- Threat intelligence & alerts
- Benchmarking and peer comparisons
- Dashboards & reporting
- Integration with risk workflows
Pros
- Strong cybersecurity focus
- Continuous updates
- Broad threat indicators
Cons
- Limited non‑cyber risk coverage
- Works best with dedicated risk workflows
Platforms / Deployment
- Web / Cloud
Security & Compliance
- Encryption, secure access
Integrations & Ecosystem
- SIEM, risk platforms
Support & Community
- Support resources
#9 — RiskRate (by NAVEX Global)
Short description:
RiskRate provides third‑party risk assessments, compliance due diligence, ongoing monitoring, issue tracking, and reporting capabilities — integrated with NAVEX GRC risk and compliance suite.
Key Features
- Risk assessments & due diligence
- Compliance questionnaires
- Monitoring & alerts
- Issue tracking
- Dashboards & reporting
Pros
- Good integrated GRC workflows
- Usable for privacy & operational risk
- Mid‑market friendly
Cons
- Smaller footprint in analytics
- Deployment planning required
Platforms / Deployment
- Web / Cloud
Security & Compliance
- Encryption, RBAC, audit logs
Integrations & Ecosystem
- GRC, procurement
Support & Community
- Support teams
#10 — RiskWatch Third Party Risk Management
Short description:
RiskWatch TPRM focuses on automated assessments, gap analysis, control scoring, risk dashboards, and compliance reporting — useful for IT, security, and operational risk teams evaluating vendors.
Key Features
- Automated risk assessments
- Gap & control scoring
- Dashboards & risk reporting
- Evidence repository
- Alerts & notifications
Pros
- Good assessment automation
- Control gap insights
- Clean dashboards
Cons
- Limited continuous monitoring
- Smaller ecosystem
Platforms / Deployment
- Web / Cloud
Security & Compliance
- Encryption, role access
Integrations & Ecosystem
- Security and compliance systems
Support & Community
- Support documentation
Comparison Table (Top 10 Third‑Party Risk Management Tools)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Ncontracts TPRM | Regulated industries | Web / Cloud | Cloud | Compliance workflows | N/A |
| Riskonnect TPRM | Enterprise risk programs | Web / Cloud | Cloud | Integrated risk suite | N/A |
| RSA Archer TPRM | Enterprise governance | Web / Cloud | Cloud | Configurable risk frameworks | N/A |
| OneTrust Vendor Risk | Privacy & compliance focus | Web / Cloud | Cloud | Control & evidence automation | N/A |
| ProcessUnity TPRM | Cloud‑native TPRM | Web / Cloud | Cloud | Assessment automation | N/A |
| SAI360 TPRM | Regulated & enterprise | Web / Cloud | Cloud | Compliance & audit | N/A |
| BitSight TPRM | Cyber risk centric | Web / Cloud | Cloud | Continuous security signals | N/A |
| SecurityScorecard TPRM | External security monitoring | Web / Cloud | Cloud | Continuous vendor security scoring | N/A |
| RiskRate | Mid‑market GRC workflows | Web / Cloud | Cloud | GRC integration | N/A |
| RiskWatch TPRM | Assessment & gaps | Web / Cloud | Cloud | Gap and control insights | N/A |
Evaluation & Scoring of Third‑Party Risk Management Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Ncontracts TPRM | 9 | 8 | 8 | 9 | 9 | 8 | 7 | 8.3 |
| Riskonnect TPRM | 8 | 8 | 8 | 9 | 8 | 8 | 8 | 8.1 |
| RSA Archer TPRM | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.3 |
| OneTrust Vendor Risk | 8 | 7 | 9 | 9 | 8 | 8 | 7 | 8.0 |
| ProcessUnity TPRM | 8 | 8 | 8 | 8 | 8 | 8 | 7 | 8.0 |
| SAI360 TPRM | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| BitSight TPRM | 8 | 8 | 7 | 8 | 8 | 8 | 8 | 8.0 |
| SecurityScorecard TPRM | 8 | 8 | 7 | 8 | 8 | 8 | 8 | 8.0 |
| RiskRate | 7 | 8 | 7 | 8 | 7 | 8 | 8 | 7.8 |
| RiskWatch TPRM | 7 | 8 | 7 | 8 | 7 | 8 | 8 | 7.8 |
Interpretation: Higher weighted totals reflect strong core third‑party risk features, broad integrations, security posture, and value for enterprise risk programs.
Which Third‑Party Risk Management Tool Is Right for You?
Enterprise & Regulated Environments
For large teams with extensive governance needs, Ncontracts TPRM, RSA Archer TPRM, or OneTrust Vendor Risk deliver strong compliance workflows, configurable risk models, and executive dashboards.
Integrated Enterprise Risk Programs
Organizations embedding third‑party risk into broader enterprise risk management will benefit from Riskonnect TPRM, ProcessUnity TPRM, or SAI360 TPRM.
Cybersecurity‑Focused Risk Insight
If vendor cyber posture is a priority, BitSight TPRM and SecurityScorecard TPRM offer continuous external security scoring and threat signals.
Mid‑Market with GRC Integration
Teams seeking risk and compliance workflows without heavy enterprise overhead may consider RiskRate or ProcessUnity TPRM for balanced functionality.
Assessment & Control Gap Focus
For teams prioritizing structured assessments and control gap insights, RiskWatch TPRM delivers clean dashboards and control scoring.
Frequently Asked Questions (FAQs)
1. What is a Third‑Party Risk Management (TPRM) tool?
It’s a platform that helps organizations manage risks introduced by external vendors/partners by standardizing assessments, controls, monitoring, and reporting across the vendor lifecycle.
2. Do TPRM tools integrate with procurement systems?
Yes — most include integrations or connectors with procurement and vendor onboarding systems so risk profiles and controls align with sourcing workflows.
3. Can these tools automate risk scoring?
Yes — leading TPRM tools provide automated risk scoring based on assessment results, continuous signals, and configured risk models.
4. Is continuous monitoring included?
Many platforms integrate with external threat feeds and compliance data sources to provide continuous risk signals and alerts.
5. Do TPRM tools support compliance frameworks?
Yes — tools often include frameworks aligned to GDPR, SOC 2, ISO standards, industry‑specific regulations, and corporate policies.
6. Are dashboards included?
Yes — modern TPRM tools offer executive and operational dashboards showing risk heatmaps, vendor panels, and trends.
7. Do they help with remediation tracking?
Yes — platforms include workflows for tracking remediation tasks, issue resolution, and control verification.
8. Can these tools scale globally?
Yes — many support multi‑region risk assessments, languages, and compliance requirements for global operations.
9. How long does implementation take?
Simple setups can launch in weeks; enterprise integrations with multiple data sources may take months.
10. Are third‑party contracts part of TPRM?
TPRM tools often integrate with contract management systems to tie risk obligations, clauses, and controls into lifecycle workflows.
Conclusion
Third‑Party Risk Management (TPRM) tools are essential for modern enterprises seeking systematic, scalable oversight of their vendor and partner ecosystems. Whether your focus is on compliance workflows, continuous cybersecurity monitoring, enterprise risk integration, or structured assessments, there’s a tool built for your context. Solutions like Ncontracts TPRM, RSA Archer TPRM, and OneTrust Vendor Risk provide robust, enterprise‑grade capabilities, while platforms like BitSight TPRM and SecurityScorecard TPRM sharpen focus on external security signals. Mid‑market teams with balanced needs can find value in RiskRate and ProcessUnity TPRM. When choosing a tool, consider your integration landscape, regulatory obligations, severity of risk exposures, and how you plan to operationalize third‑party risk to ensure your choice drives measurable governance, compliance, and operational resilience.