Find the Best Cosmetic Hospitals — Choose with Confidence
Discover top cosmetic hospitals in one place and take the next step toward the look you’ve been dreaming of.
“Your confidence is your power — invest in yourself, and let your best self shine.”
Compare • Shortlist • Decide smarter — works great on mobile too.
Introduction
Secure software supply chain attestation tools help organizations prove how software was built, where it came from, who built it, what dependencies were used, and whether the build process followed trusted controls. In simple terms, these tools create verifiable evidence for software artifacts so teams can reduce the risk of tampered builds, malicious packages, dependency confusion, and unauthorized releases.This category matters because modern software is no longer built from one codebase alone. Applications depend on open-source libraries, CI/CD pipelines, containers, build systems, package registries, and cloud infrastructure. Without strong provenance and attestation, security teams may struggle to verify whether an artifact is trustworthy before deployment.
Common real-world use cases include:
- Generating provenance for builds and releases
- Signing container images and software artifacts
- Verifying CI/CD pipeline integrity
- Enforcing SLSA-style software supply chain controls
- Auditing open-source dependency risk
- Securing Kubernetes and cloud-native deployments
Buyers should evaluate:
- Artifact signing support
- Provenance generation
- SLSA alignment
- SBOM support
- CI/CD integration
- Policy enforcement
- Container registry compatibility
- Kubernetes admission control
- Developer experience
- Auditability and compliance readiness
Best for: DevSecOps teams, platform engineering teams, security architects, software vendors, regulated organizations, cloud-native teams, and enterprises that need verifiable software build integrity.
Not ideal for: very small teams with simple manual deployments, organizations without CI/CD maturity, or teams that only need basic vulnerability scanning rather than full artifact provenance and attestation.
Key Trends in Secure Software Supply Chain Attestation Tools
- Software provenance is becoming a core requirement for enterprise software delivery.
- SLSA-style controls are influencing how teams design trusted build pipelines.
- Artifact signing is becoming common for containers, binaries, packages, and releases.
- SBOM generation is increasingly paired with attestation and policy enforcement.
- Kubernetes admission control is being used to block unsigned or untrusted workloads.
- CI/CD-native security checks are moving earlier into developer workflows.
- Open-source tools are gaining strong adoption due to transparency and flexibility.
- Enterprises are combining signing, provenance, vulnerability scanning, and policy-as-code.
- Build systems are shifting toward hermetic, reproducible, and auditable pipelines.
- Security teams are focusing more on tamper evidence, not just vulnerability detection.
How We Selected These Tools Methodology
The tools in this list were selected based on practical relevance for software supply chain security, provenance, attestation, and artifact trust.
Selection factors included:
- Adoption across DevSecOps and platform engineering teams
- Support for signing, provenance, SBOMs, or attestations
- Alignment with SLSA-style security practices
- CI/CD and developer workflow compatibility
- Container and Kubernetes ecosystem support
- Policy enforcement capabilities
- Open-source community strength
- Enterprise deployment suitability
- Documentation and onboarding quality
- Fit across startups, SMBs, mid-market teams, and enterprises
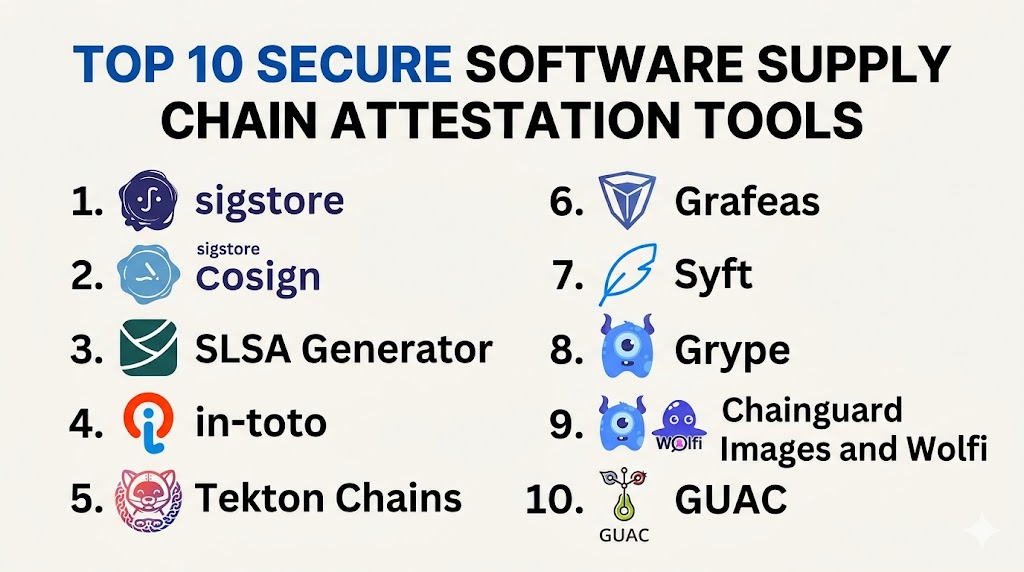
Top 10 Secure Software Supply Chain Attestation Tools
#1 — Sigstore
Short description: Sigstore is an open-source ecosystem for signing, verifying, and protecting software artifacts. It is widely used for keyless signing, transparency logs, and artifact trust across modern software supply chains. Sigstore is especially useful for teams that want to verify container images, packages, binaries, and build outputs without managing traditional long-lived signing keys. It is a strong fit for DevSecOps teams building provenance-based security workflows.
Key Features
- Keyless software signing
- Transparency log support
- Artifact verification
- Container image signing
- Certificate-based identity model
- CI/CD workflow integration
- Support for provenance and attestations
Pros
- Strong open-source ecosystem adoption
- Reduces complexity of key management
- Works well with cloud-native software delivery
Cons
- Requires teams to understand signing workflows
- Enterprise governance needs careful planning
- Policy enforcement usually requires additional tools
Platforms / Deployment
- Linux / macOS / Windows
- Cloud / Self-hosted / Hybrid
Security & Compliance
- Artifact signing
- Transparency logging
- Identity-based signing
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
Sigstore integrates well with container registries, CI/CD pipelines, Kubernetes workflows, and open-source packaging ecosystems.
- GitHub Actions
- Kubernetes
- Container registries
- Cosign
- Rekor
- Fulcio
Support & Community
Sigstore has a strong open-source community and broad ecosystem visibility. Documentation is mature for developers, but enterprise rollout may require platform engineering support.
#2 — Cosign
Short description: Cosign is a widely used artifact signing and verification tool from the Sigstore ecosystem. It is commonly used to sign container images, verify signatures, attach attestations, and secure deployment pipelines. Cosign is especially valuable for teams adopting Kubernetes and container-native software supply chain controls. It gives security teams a practical way to enforce artifact trust before deployment.
Key Features
- Container image signing
- Keyless signing support
- Signature verification
- Attestation support
- SBOM attachment support
- Registry integration
- Kubernetes policy compatibility
Pros
- Practical and developer-friendly
- Strong container ecosystem support
- Works well with admission control workflows
Cons
- Focused mainly on artifact signing and verification
- Policy management requires separate tooling
- Teams need process maturity to use it effectively
Platforms / Deployment
- Linux / macOS / Windows
- Cloud / Self-hosted / Hybrid
Security & Compliance
- Artifact signing
- Keyless signing support
- Signature verification
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
Cosign works closely with container registries, Kubernetes environments, and CI/CD pipelines.
- Docker registries
- OCI registries
- Kubernetes admission controllers
- GitHub Actions
- Tekton
- Sigstore ecosystem
Support & Community
Cosign has strong community support and is widely referenced in cloud-native security workflows. Documentation is practical and useful for DevSecOps teams.
#3 — SLSA Generator
Short description: SLSA Generator helps teams generate provenance for build artifacts in alignment with SLSA-style software supply chain security practices. It is useful for organizations that want structured evidence about how software was built and which workflow produced it. The tool is especially relevant for teams using automated CI/CD pipelines and looking to improve build integrity. It provides a practical path toward stronger provenance without building everything from scratch.
Key Features
- Provenance generation
- Build workflow attestation
- CI/CD integration
- SLSA-aligned metadata
- Artifact identity tracking
- Source-to-build linkage
- Release evidence support
Pros
- Purpose-built for provenance workflows
- Helpful for SLSA adoption
- Good fit for automated build pipelines
Cons
- Requires CI/CD process discipline
- May not cover all custom build systems
- Works best when paired with signing and policy tools
Platforms / Deployment
- Linux / macOS / Windows
- Cloud / Self-hosted / Hybrid
Security & Compliance
- Provenance generation
- Build metadata attestation
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
SLSA Generator fits into build workflows where teams need to produce trusted evidence for artifacts.
- GitHub Actions
- Build pipelines
- Artifact repositories
- Release workflows
- Signing tools
Support & Community
Community support is strongest among teams actively adopting SLSA practices. Documentation is useful for security-focused build pipeline teams.
#4 — in-toto
Short description: in-toto is a software supply chain security framework that helps define, record, and verify each step in the software delivery process. It allows teams to create metadata showing which actors performed which steps, from source code to final artifact. in-toto is valuable for teams that need end-to-end supply chain integrity and detailed verification. It is especially useful in regulated or high-assurance software environments.
Key Features
- Supply chain layout definitions
- Step-by-step metadata recording
- Artifact verification
- Cryptographic signing
- Policy-based validation
- Provenance support
- Strong audit trail capability
Pros
- Excellent end-to-end verification model
- Strong fit for high-assurance workflows
- Flexible and standards-oriented
Cons
- Setup can be complex
- Requires process design effort
- Developer onboarding may take time
Platforms / Deployment
- Linux / macOS / Windows
- Self-hosted / Hybrid
Security & Compliance
- Cryptographic signing
- Metadata verification
- Audit trail support
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
in-toto integrates with build systems, signing tools, CI/CD pipelines, and policy workflows.
- CI/CD tools
- Build systems
- Package workflows
- Sigstore ecosystem
- SLSA-related workflows
Support & Community
in-toto has a strong security research and open-source community. It is well suited for teams with mature DevSecOps practices.
#5 — Tekton Chains
Short description: Tekton Chains is a Kubernetes-native tool that generates and signs provenance for Tekton pipeline runs. It is designed for teams using Tekton as their CI/CD foundation and wanting trusted metadata for build artifacts. Tekton Chains helps connect build execution, signatures, and provenance records in cloud-native environments. It is especially useful for platform teams standardizing secure CI/CD on Kubernetes.
Key Features
- Pipeline provenance generation
- Artifact signing
- Kubernetes-native architecture
- Tekton integration
- OCI registry support
- Build metadata capture
- Policy enforcement compatibility
Pros
- Strong fit for Tekton users
- Kubernetes-native design
- Good provenance automation
Cons
- Best suited only for Tekton-based pipelines
- Requires Kubernetes expertise
- Less useful for non-Tekton CI/CD systems
Platforms / Deployment
- Linux / Kubernetes
- Cloud / Self-hosted / Hybrid
Security & Compliance
- Artifact signing
- Provenance generation
- Kubernetes-native metadata
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
Tekton Chains works deeply within Kubernetes and Tekton-based software delivery pipelines.
- Tekton Pipelines
- Kubernetes
- OCI registries
- Cosign
- Sigstore
- Cloud-native CI/CD systems
Support & Community
Support is strongest in the Kubernetes and Tekton communities. Teams already using Tekton will find the onboarding path more natural.
#6 — Grafeas
Short description: Grafeas is an open-source metadata API for storing and querying software supply chain metadata. It helps organizations track information such as build details, vulnerability data, deployment metadata, and attestations. Grafeas is useful for teams that want a central evidence store for software artifacts across environments. It works best as part of a broader supply chain security architecture.
Key Features
- Metadata storage API
- Artifact history tracking
- Build metadata support
- Vulnerability metadata support
- Attestation storage
- Policy workflow compatibility
- Centralized evidence management
Pros
- Useful for centralized metadata governance
- Flexible API-driven model
- Strong fit for enterprise evidence tracking
Cons
- Not a complete signing tool by itself
- Requires integration work
- Needs additional enforcement tools
Platforms / Deployment
- Linux / Cloud environments
- Cloud / Self-hosted / Hybrid
Security & Compliance
- Metadata tracking
- Attestation support
- Access control depends on implementation
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
Grafeas fits well into enterprise software supply chain visibility and governance architectures.
- CI/CD systems
- Artifact registries
- Vulnerability scanners
- Policy engines
- Cloud-native platforms
Support & Community
Community support is more specialized and platform-focused. It is best suited for teams building custom supply chain security platforms.
#7 — Syft
Short description: Syft is an open-source SBOM generation tool that helps teams identify software components inside containers, filesystems, and packages. While it is not only an attestation tool, it is highly relevant because SBOMs are often attached to signed artifacts and provenance workflows. Syft is useful for DevSecOps teams that need visibility into dependencies before signing, releasing, or deploying software. It pairs well with scanning, signing, and policy tools.
Key Features
- SBOM generation
- Container image analysis
- Filesystem scanning
- Package detection
- Multiple SBOM format support
- CI/CD integration
- Works with related security tools
Pros
- Strong dependency visibility
- Easy to integrate into pipelines
- Useful for compliance preparation
Cons
- Does not enforce policy by itself
- Not a full provenance platform
- Needs signing tools for attestation workflows
Platforms / Deployment
- Linux / macOS / Windows
- Cloud / Self-hosted / Hybrid
Security & Compliance
- SBOM generation
- Dependency inventory support
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
Syft integrates easily into DevSecOps pipelines and artifact security workflows.
- GitHub Actions
- Docker
- Kubernetes workflows
- Grype
- Cosign
- CI/CD systems
Support & Community
Syft has strong open-source community adoption and practical documentation for security and DevOps teams.
#8 — Grype
Short description: Grype is an open-source vulnerability scanner commonly used alongside SBOM and attestation workflows. It scans container images, filesystems, and software packages for known vulnerabilities. While Grype is not a provenance tool by itself, it strengthens supply chain attestation by helping teams validate artifact risk before release. It is often paired with Syft, Cosign, and CI/CD policy gates.
Key Features
- Vulnerability scanning
- Container image analysis
- SBOM-based scanning
- CI/CD pipeline support
- Multiple package ecosystem coverage
- Developer-friendly CLI
- Risk visibility for release decisions
Pros
- Easy to use in pipelines
- Strong pairing with SBOM workflows
- Helps improve release confidence
Cons
- Not an attestation platform alone
- Vulnerability results need governance
- False positives require review
Platforms / Deployment
- Linux / macOS / Windows
- Cloud / Self-hosted / Hybrid
Security & Compliance
- Vulnerability detection
- SBOM scan support
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
Grype works well with SBOM tools and CI/CD systems to strengthen artifact verification workflows.
- Syft
- GitHub Actions
- Docker
- Container registries
- CI/CD pipelines
- Kubernetes workflows
Support & Community
Grype has active open-source community support and is commonly used by DevSecOps teams.
#9 — Chainguard Images and Wolfi
Short description: Chainguard Images and Wolfi support secure software supply chain practices through minimal, hardened container images and a security-focused Linux distribution model. These tools help teams reduce attack surface and improve artifact trust. They are especially valuable for organizations seeking secure base images, improved provenance, and stronger container supply chain hygiene. The platform is useful for teams that want safer production containers from the beginning.
Key Features
- Minimal container images
- Security-focused package ecosystem
- Provenance-oriented workflows
- Reduced attack surface
- Container supply chain hardening
- SBOM support
- Cloud-native deployment fit
Pros
- Strong focus on secure-by-default images
- Useful for reducing container risk
- Good fit for Kubernetes workloads
Cons
- May require image migration effort
- Ecosystem fit depends on application stack
- Commercial support details vary
Platforms / Deployment
- Linux / Kubernetes / Container platforms
- Cloud / Self-hosted / Hybrid
Security & Compliance
- SBOM support
- Secure image model
- Provenance support varies by implementation
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
Chainguard Images and Wolfi fit into container security, Kubernetes, and DevSecOps workflows.
- Kubernetes
- Container registries
- CI/CD pipelines
- SBOM tools
- Signing workflows
- Cloud-native platforms
Support & Community
Community and commercial support vary by offering. Documentation is practical for teams adopting secure container images.
#10 — GUAC
Short description: GUAC is a software supply chain metadata platform designed to collect, normalize, and analyze metadata from different security tools and artifact sources. It helps teams understand relationships between packages, vulnerabilities, SBOMs, repositories, and artifacts. GUAC is useful for organizations that need deeper visibility across complex software supply chains. It works best as an intelligence layer rather than a standalone signing tool.
Key Features
- Supply chain metadata aggregation
- SBOM ingestion
- Dependency relationship mapping
- Vulnerability context
- Artifact graph analysis
- API-driven architecture
- Risk investigation support
Pros
- Strong visibility across supply chain data
- Useful for complex environments
- Helps connect SBOM and vulnerability context
Cons
- Requires integration effort
- Not a direct signing tool
- Best suited for mature security teams
Platforms / Deployment
- Linux / Cloud environments
- Self-hosted / Hybrid
Security & Compliance
- Metadata analysis
- Supply chain visibility
- Access controls vary by implementation
- Compliance certifications: Not publicly stated
Integrations & Ecosystem
GUAC integrates with SBOM sources, vulnerability data, package metadata, and software artifact systems.
- SBOM tools
- Vulnerability scanners
- Package repositories
- CI/CD pipelines
- Artifact metadata sources
- Security analytics workflows
Support & Community
GUAC has growing community interest among software supply chain security teams. It is best suited for teams with mature metadata and analysis needs.
Comparison Table Top 10
| Tool Name | Best For | Platform Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Sigstore | Keyless software signing | Linux, macOS, Windows | Cloud, Self-hosted, Hybrid | Transparency-based signing | N/A |
| Cosign | Container image signing | Linux, macOS, Windows | Cloud, Self-hosted, Hybrid | OCI artifact signing | N/A |
| SLSA Generator | Build provenance | Linux, macOS, Windows | Cloud, Self-hosted, Hybrid | SLSA-aligned provenance | N/A |
| in-toto | End-to-end supply chain verification | Linux, macOS, Windows | Self-hosted, Hybrid | Step-by-step metadata verification | N/A |
| Tekton Chains | Kubernetes-native CI/CD provenance | Linux, Kubernetes | Cloud, Self-hosted, Hybrid | Tekton pipeline attestation | N/A |
| Grafeas | Metadata storage and governance | Linux, Cloud environments | Cloud, Self-hosted, Hybrid | Central metadata API | N/A |
| Syft | SBOM generation | Linux, macOS, Windows | Cloud, Self-hosted, Hybrid | Dependency inventory creation | N/A |
| Grype | Vulnerability scanning | Linux, macOS, Windows | Cloud, Self-hosted, Hybrid | SBOM-based vulnerability scanning | N/A |
| Chainguard Images and Wolfi | Secure container base images | Linux, Kubernetes | Cloud, Self-hosted, Hybrid | Minimal trusted images | N/A |
| GUAC | Supply chain metadata analysis | Linux, Cloud environments | Self-hosted, Hybrid | Artifact relationship graph | N/A |
Evaluation & Scoring of Secure Software Supply Chain Attestation Tools
| Tool Name | Core 25% | Ease 15% | Integrations 15% | Security 10% | Performance 10% | Support 10% | Value 15% | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Sigstore | 9 | 7 | 9 | 9 | 8 | 8 | 9 | 8.45 |
| Cosign | 9 | 8 | 9 | 9 | 8 | 8 | 9 | 8.60 |
| SLSA Generator | 8 | 7 | 8 | 8 | 8 | 7 | 8 | 7.75 |
| in-toto | 9 | 6 | 8 | 9 | 7 | 7 | 8 | 7.85 |
| Tekton Chains | 8 | 6 | 8 | 8 | 8 | 7 | 8 | 7.55 |
| Grafeas | 7 | 6 | 7 | 7 | 7 | 6 | 7 | 6.75 |
| Syft | 8 | 9 | 8 | 7 | 8 | 8 | 9 | 8.10 |
| Grype | 8 | 9 | 8 | 7 | 8 | 8 | 9 | 8.10 |
| Chainguard Images and Wolfi | 8 | 7 | 8 | 9 | 8 | 8 | 8 | 8.00 |
| GUAC | 8 | 6 | 8 | 8 | 7 | 7 | 8 | 7.55 |
These scores are comparative and should be interpreted based on your organization’s needs. A higher score does not mean the tool is universally better; it means the tool performs strongly across the chosen criteria. Some tools focus on signing, others focus on SBOMs, vulnerability scanning, metadata storage, or secure base images. The best approach is often a combination of tools rather than one single platform.
Which Secure Software Supply Chain Attestation Tool Is Right for You?
Solo / Freelancer
Solo developers should start with practical and lightweight tools such as Cosign, Syft, and Grype. These tools are easy to add into local workflows and CI/CD pipelines without building a large security program. Cosign helps sign artifacts, Syft generates SBOMs, and Grype helps identify known vulnerabilities before release.
SMB
SMBs should focus on simple, high-value controls that improve trust without overwhelming teams. Cosign, Sigstore, Syft, and Grype provide a strong starting stack. If the team uses GitHub Actions or similar CI/CD tools, adding SLSA Generator can improve provenance without creating too much operational complexity.
Mid-Market
Mid-market organizations should build a more structured attestation workflow around signing, SBOMs, vulnerability scanning, and policy checks. Sigstore, Cosign, in-toto, Tekton Chains, and Chainguard Images can provide stronger governance. Teams should also begin documenting release evidence and build integrity requirements.
Enterprise
Enterprises need scalable governance, auditability, policy enforcement, and metadata visibility. A strong enterprise stack may include Sigstore, Cosign, in-toto, Grafeas, GUAC, and secure base images from Chainguard Images and Wolfi. Enterprises should prioritize build pipeline trust, artifact verification, admission control, and centralized metadata.
Budget vs Premium
Open-source tools such as Sigstore, Cosign, Syft, Grype, in-toto, and GUAC are strong options for budget-conscious teams. Premium value usually comes from managed support, secure image subscriptions, enterprise dashboards, policy management, and support SLAs. Teams should begin with open-source controls, then add premium support where operational risk is highest.
Feature Depth vs Ease of Use
Cosign, Syft, and Grype are easier to adopt quickly. in-toto, Grafeas, and GUAC provide deeper supply chain visibility but require more planning and integration. Teams with limited security engineering capacity should start simple and gradually move toward deeper attestation workflows.
Integrations & Scalability
Organizations using Kubernetes, containers, and CI/CD pipelines should prioritize tools that integrate naturally into those environments. Cosign, Sigstore, Tekton Chains, Syft, Grype, and Chainguard Images are strong fits for cloud-native teams. For large-scale metadata visibility, GUAC and Grafeas can help connect security evidence across systems.
Security & Compliance Needs
For strict security and compliance needs, prioritize tools that generate verifiable evidence, sign artifacts, support SBOMs, and integrate with policy enforcement. Sigstore, Cosign, in-toto, SLSA Generator, and Tekton Chains are strong choices for attestation-driven controls. Enterprises should also validate audit logs, access controls, retention policies, and approval workflows.
Frequently Asked Questions FAQs
1. What are software supply chain attestation tools?
Software supply chain attestation tools create proof about how software was built, signed, scanned, and released. They help teams verify whether an artifact came from a trusted source and followed approved build steps. This is important because modern software depends on many external packages, automated pipelines, and container images. Attestation gives teams evidence they can use before deployment.
2. What is SLSA in software supply chain security?
SLSA is a framework for improving software build integrity and reducing supply chain risk. It focuses on areas such as provenance, trusted build systems, source integrity, and tamper-resistant release processes. Teams use SLSA-style practices to make software builds more transparent and verifiable. Tools like SLSA Generator help produce provenance metadata for this purpose.
3. What is software provenance?
Software provenance is information that explains where a software artifact came from and how it was created. It may include source repository details, build workflow data, builder identity, dependencies, and output artifact information. Provenance helps security teams verify whether software was produced by an authorized and trusted process. It is a core part of modern attestation workflows.
4. Are SBOM tools the same as attestation tools?
No, SBOM tools and attestation tools are related but not identical. SBOM tools list the components and dependencies inside software, while attestation tools provide evidence about build and release processes. In practice, both are often used together. A team may generate an SBOM with Syft, scan it with Grype, and then attach it to a signed artifact using Cosign.
5. Which tool is best for container image signing?
Cosign is one of the most practical and widely used tools for container image signing. It works well with OCI registries and modern CI/CD workflows. Teams can use it to sign images, verify signatures, and attach attestations. It is often used with Sigstore components for keyless signing and transparency logging.
6. How difficult is it to implement supply chain attestation?
Implementation difficulty depends on CI/CD maturity and existing release processes. Teams with automated builds can start by adding SBOM generation, vulnerability scanning, artifact signing, and provenance generation. Manual or inconsistent release processes will need more cleanup before attestation becomes reliable. A phased rollout is usually the best approach.
7. What are common mistakes when adopting these tools?
A common mistake is treating signing as a checkbox without enforcing verification before deployment. Another mistake is generating SBOMs but not storing, reviewing, or using them in policy decisions. Teams also sometimes adopt too many tools at once without defining ownership. Successful adoption requires clear workflows, policy rules, developer training, and ongoing review.
8. Can these tools help with compliance?
Yes, these tools can support compliance by creating evidence about builds, dependencies, vulnerabilities, signatures, and release processes. However, they do not automatically guarantee compliance by themselves. Organizations still need policies, approvals, access controls, audit trails, and documentation. Attestation tools make compliance evidence easier to collect and verify.
9. Do small teams need software supply chain attestation?
Small teams may not need a complex enterprise-grade attestation platform immediately, but they should still adopt basic controls. Signing releases, generating SBOMs, and scanning artifacts can reduce risk significantly. Tools like Cosign, Syft, and Grype are practical starting points. As the team grows, provenance and policy enforcement can be added gradually.
10. What is the best way to start with SLSA and provenance?
The best starting point is to identify critical build pipelines and add basic provenance generation, artifact signing, SBOM creation, and vulnerability scanning. Teams should then verify artifacts before deployment and document which controls are required for production releases. After the basics are stable, they can add stronger policy enforcement, centralized metadata, and advanced attestation workflows.
Conclusion
Secure software supply chain attestation tools are becoming essential for teams that want to prove software integrity from source code to production deployment. The best solution depends on whether your priority is artifact signing, SBOM generation, vulnerability scanning, build provenance, metadata governance, or secure container images. Cosign and Sigstore are strong starting points for signing and verification, while SLSA Generator and in-toto help teams improve provenance and process integrity. Syft and Grype strengthen dependency and vulnerability visibility, while GUAC and Grafeas support deeper metadata analysis for larger environments. Chainguard Images and Wolfi help teams reduce container risk at the base image level. The smartest approach is not to look for one universal winner, but to build a practical stack around your CI/CD pipelines, artifact registries, Kubernetes workflows, and compliance needs. Start with a shortlist, run a controlled pilot, validate integrations and security controls, then scale the attestation program across high-risk software delivery paths.